The average luxury car contains more lines of code than the Boeing 787 Dreamliner, F-35 Joint Strike Fighter, and F-22 Raptor combined. This amount of code is the engine that pushes the automotive industry forward, but it also exposes it to new vulnerabilities and cyber risks.
Car hackers and thieves keep up with automotive software improvements and create technologically advanced ways to steal vehicles. Manufacturers also have to evolve and protect their vehicles from cyber attacks. The first step is comprehensive security testing that helps to detect vulnerabilities in a vehicle’s code at early stages.
Conducting security testing for automotive software requires knowledge of industry requirements, challenges, and best practices. In this article, we discuss how to secure automotive software and why security testing is so important.
This article will be useful for development teams and their leaders who are working on automotive software and need to examine its security.
Contents:
Why pay attention to vehicle software security?
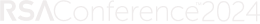
Modern cars are no longer standalone mechanical systems. They are connected with the outside world via numerous electronic control units (ECUs). Cars use complex software to ensure safe travel, enable autonomous driving, entertain passengers, perform car diagnostics, etc.
Such smart features are appreciated by car buyers, which is why demand for automotive software grows by the minute. McKinsey estimates that the market for automotive software and electronics will grow from $238 billion in 2020 to $469 billion in 2030.
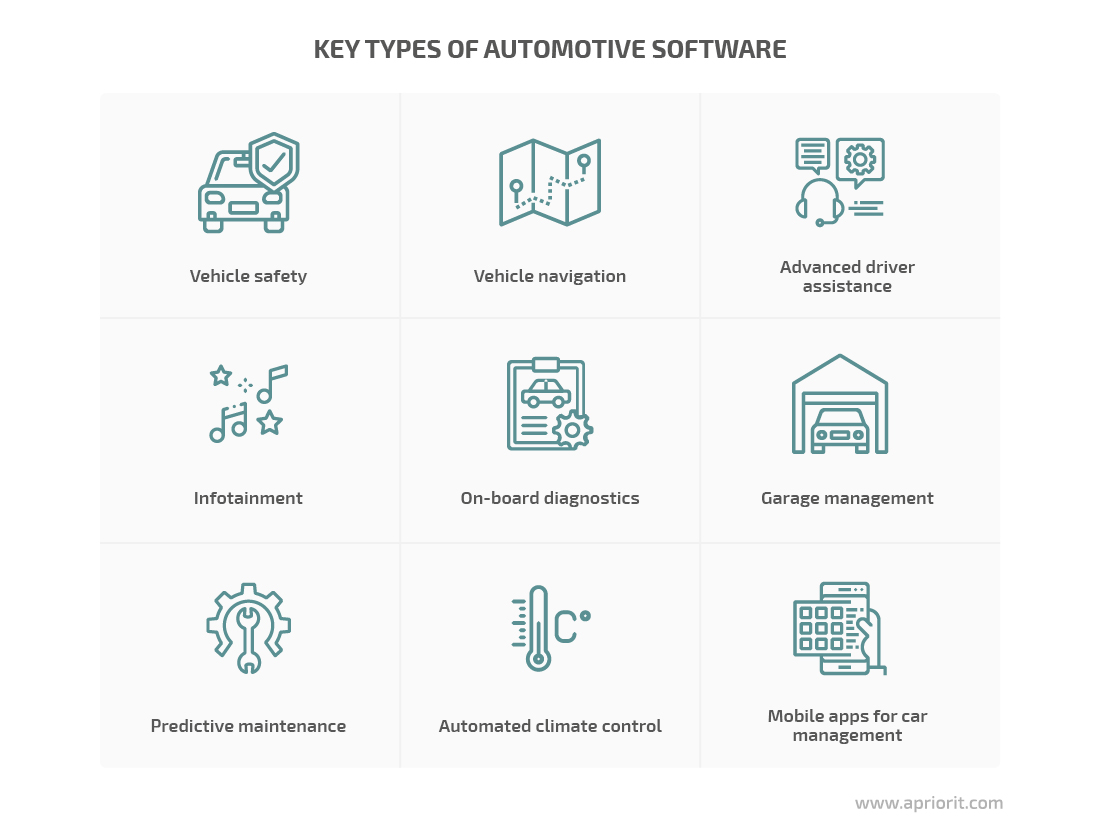
While innovative software pushes the automotive industry forward, it also makes cars more vulnerable to hacking attacks. Hackers may abuse poorly protected automotive software to steal or take control of:
- victims’ personal data and finances
- cargo shipped by compromised vehicles
- vehicles themselves
In 2021 alone, we’ve seen a lot of automotive security breaches. For example, in May 2021, two security researchers hacked a Tesla Model X in just 40 minutes using a drone equipped with a Wi-Fi dongle. The researchers could open and close the target car’s doors, change driving and acceleration settings, and so on. And that’s not the first Tesla hack, despite the fact that the company pays a lot of attention to cybersecurity.
Another example of a widespread security breach is breaking into cars equipped with keyless entry systems. In Columbus, Ohio, hackers simulated signals from key fobs and stole 43 cars from the same neighborhood in two months. They did it without triggering the cars’ alarms or even touching key fobs.
All these cases prove that ensuring proper security of automotive software should be a top priority for car manufacturers and logistics companies. Not paying enough attention to this matter may result in lots of negative consequences for vehicle manufacturers.
Designing automotive software with cybersecurity in mind decreases the probability of car hacking and associated risks. And one of the first steps towards ensuring proper security of your automotive software is getting it in line with industry and national requirements. Let’s take a look at automotive software security requirements you can follow to secure your product.
Read also:
Artificial Intelligence in the Automotive Industry: 6 Key Applications for a Competitive Advantage
What are the requirements for securing automotive software?
To improve security and prevent hacks, many governments and international organizations are working on guidelines and requirements for the development of secure automotive software. You can follow these to implement security best practices while working on in-vehicle solutions:
- Cybersecurity Best Practices for the Safety of Modern Vehicles by the US National Highway Traffic Safety Administration. These practices are non-binding, and they will be updated with new tips by the end of 2021.
- UN regulations Nos. 155, 156, and 157 describe requirements for vehicle cybersecurity, security management, and software updates and will become mandatory for UNECE member countries in the UN in July 2024.
- The draft of Provisions on Management of Automotive Data Security by the Cyberspace Administration of China. It’s planned that these rules will be implemented in 2021 and become mandatory.
- ISO/SAE 21434. This standard is currently under development and will be non-binding. It describes best practices for the development, production, operation, maintenance, and disposal of vehicles.
- SAE J3061. This guidebook contains guidelines and recommended practices for designing and developing vehicle systems to protect them from hacking attacks during a vehicle’s lifetime.

One way to check if your solution meets key requirements of relevant security standards and guidelines is by running a thorough security test of your automotive software at different stages of its development.
Automotive security testing can help you achieve several cybersecurity goals:
- Identify potential software vulnerabilities
- Test the protection of your solutions against relevant attack vectors
- Check automotive software for unexpected behavior
- Ensure correct integration of multiple software components
Security testing of complete automotive systems helps to check that all protection measures are working properly, detect vulnerabilities, and reduce the risks we mentioned earlier.
When conducting security testing of automotive systems, it’s important to ensure that the software isn’t susceptible to common attack vectors. In the next section, we take a look at the eight most common vectors of attack against modern vehicles.
Common attack vectors for automotive software
The average car contains more than a hundred ECUs that run some sort of software, and hackers can attack any of these. But cybercriminals are mostly interested in the parts of a vehicle that grant them access to valuable data or hand over full control of the entire vehicle.
Let’s look at the key attack vectors for automotive software:

Keyless entry systems. Many modern vehicles use a keyless fob instead of a traditional key. This fob transmits a short-wave radio signal and when the car’s receiver picks it up, it unlocks the doors, starts the engine, or initiates some other action. Key fobs are convenient for drivers, but they’re also easy for criminals to abuse. Criminals can use a relay device to transmit a signal from the fob to the car, even if they are far apart. Insurance research by Liverpool Victoria indicates that 48% of all vehicle theft claims are keyless thefts of Tesla, BMW, Jaguar, Lexus, and other luxury makes.
Vehicle mobile apps. Mobile apps offer drivers improved navigation, car climate control, autonomous parking, remote unlocking, entertainment, and lots of other convenient features. They can also be used for arranging car sharing and fleet management. However, hackers may compromise these features by bypassing the signature verification system, installing their own signature, and providing an application with root access. And through a compromised vehicle mobile app, criminals can steal credentials saved in the vehicle app, and further abuse both a vehicle and the devices synchronized with it.
Car manufacturer servers. The number of car manufacturer server attacks grew 73% in 2020 compared to 2019 according to Upstream Security. Manufacturer servers process all communications both inside and outside a vehicle, including communications with drivers’ mobile devices as well as other vehicles. That’s a lucrative attack surface for malicious actors. Attackers can infect a target server with ransomware, intercept transmitted data, or perform a denial of service (DoS) attack. In this way, hackers can steal sensitive data or disrupt the work of automotive services.
Car sensors. Sensors collect information on the environment around a car like the weather, road markings, tire pressure, engine rotation, and fuel temperature. Using sensor spoofing or signal jamming, hackers can change a vehicle’s behavior. They can also capture sensor signals and reverse engineer them to learn about a car’s internal systems.
Infotainment system. This system provides a driver and passengers with useful information and entertaining content. Infotainment systems accumulate tons of personal data: credentials, browsing histories, travel itineraries, personal preferences. Malicious actors can intercept traffic from an infotainment system and mess with its settings. In this way, they can steal a driver’s sensitive data.
Wi-Fi, Bluetooth, and cellular connections. Network connectivity systems can become entry points for hackers to the infotainment system. From there, they can access critical car components, influence vehicle behavior, or steal transmitted data. By compromising network connections, hackers can even attack several cars at once.
In-vehicle networks. These networks consist of ECUs and control area network (CAN) buses that work in real time. By design, ECUs and CAN buses first accept any data, then validate it and send it to other vehicle components. If software developers don’t implement data encryption at this point, hackers can take advantage of this data processing mechanism. They can abuse it and flood in-vehicle networks with packets of garbage data, creating a DoS attack, or sniff the traffic and extract sensitive data from it.
On-board diagnostics (OBD), SD card, and USB ports. Attacking in-vehicle OBD or USB ports is a less widespread type of attack, since it requires physical access to a port on the target vehicle. However, attackers can do a lot of damage via in-vehicle ports: inject devices with malware, take control of a vehicle, hijack traffic, or get access to various vehicle components.
As you can see, these attacks often target specific weaknesses and vulnerabilities hidden in automotive software and embedded in-vehicle systems. To make sure that cybercriminals won’t be able to take advantage of your automotive software solutions, you need to make sure you detect and address these security issues before you release your product to the market. And this is where automotive software security testing comes into play.
Best practices to test automotive cybersecurity
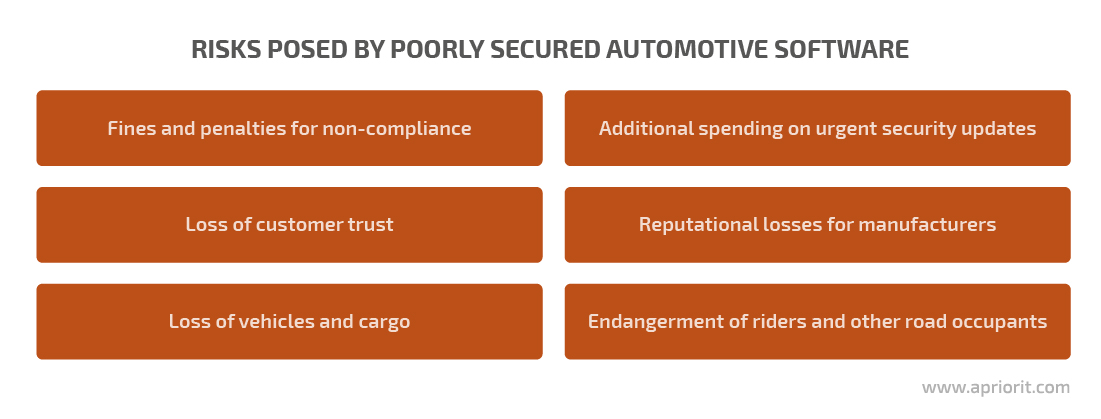
To verify the security of your automotive software, consider following these seven best practices:
Research and follow the latest cybersecurity requirements. As we mentioned above, many governments and standardization institutions are working on requirements for automotive software security. That’s why you need to constantly keep an eye on emerging laws, regulations, and standards. It also makes sense to pay attention to those that are still under development or discussion. Since the vehicle production cycle lasts several years, you might need to take these requirements into account during pre-release security testing.
Synchronize production, development, and testing. Automotive security needs to be tested in parallel with software development and car production processes. This way, a security testing team can detect vulnerabilities during development and avoid major code rework. It’s also important to test security and software behavior on physical vehicle hardware. To synchronize these activities, you can implement flexible project management approaches like Agile and Scrum.
Apply fuzz testing. Injecting vehicle software components with random data and looking for glitches is an efficient security testing technique called fuzz testing, or fuzzing. Fuzz testing is a reliable way to find hackable bugs and code errors which, if left unaddressed, may lead to software crashes, behavior changes, and memory and data leaks, or that may even serve as potential backdoors.
Analyze software composition. Automotive software is often developed by several third-party vendors that use open-source code to deliver components in time. Some of those open-source components may contain known vulnerabilities and become an entryway for malicious actors. Manually discovering all open-source libraries and solutions used to build your automotive software is extremely time-consuming and subject to human error. Software composition analysis tools can do that automatically for your testing team.
Pay extra attention to integration testing. Considering how many automotive software components are developed by different teams or even organizations, there’s a high chance of unexpected interactions between them. These interactions can hide potential threats, such as establishing an unprotected connection or accepting data from unknown sources. That’s why automotive software requires careful integration testing of all components.
Conduct penetration testing. Automotive penetration testing emulates an attack on automotive software in an attempt to find any vulnerabilities and assess the potential damage from an attack. Pentesting services can be provided by an in-house security testing team that knows the software well or by an outside team that can analyze your product from a new angle.
Update your software regularly. Hackers will more likely target cars with outdated software because they already know everything about security vulnerabilities in that software. That’s why you need to test your code against new types of attacks periodically and roll out new security updates.
Following these best practices will help you optimize the security testing process, detect more vulnerabilities in code, and release secure software. However, there are several challenges with testing the security of automotive software that you need to be aware of. Let’s take a look at them.
Challenges of security testing in automotive
With unique testing conditions and practices come unique challenges your QA team may face. Part of these challenges are related to integral characteristics of the automotive industry that you need to take into account while planning security testing. But some can be mitigated or even avoided with the correct approach to testing.
Let’s take a look at the key challenges of conducting security testing on an automotive project and ways to deal with them.
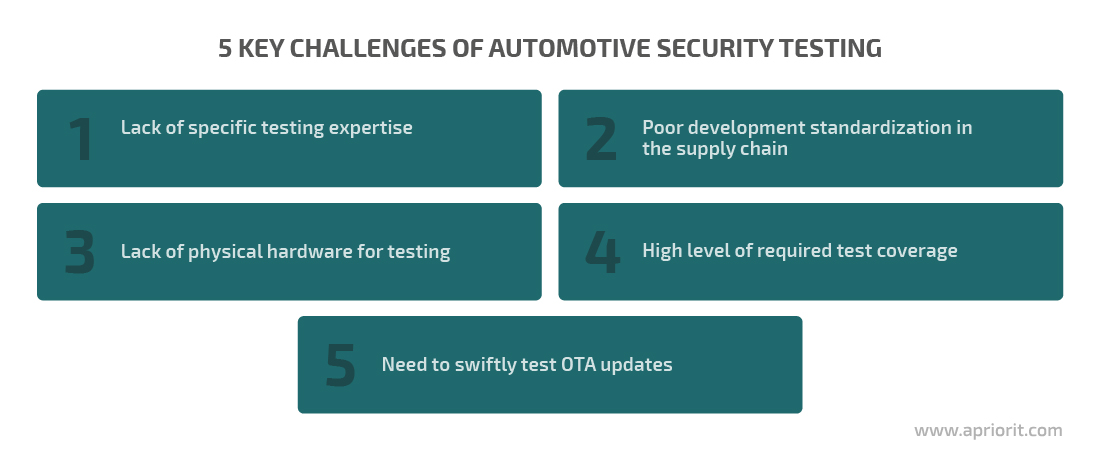
Lack of specific testing expertise. Full-scale security testing of automotive software includes checking the protection of embedded, IoT, mobile, virtual, cloud-based, and client–server systems. Advanced automotive systems can also employ artificial intelligence (AI) algorithms for predictive maintenance and autopilot. Security testers and testing teams with expert skills in all of these areas are extremely rare. That’s why it can be a challenge to create a full-stack team in-house or quickly hire an engineer with the required skills. One solution to this challenge is to look for outsourcing teams that possess the needed expertise.
To learn more about artificial intelligence use cases, check out our article about using AI in the automotive industry.
Lack of physical hardware for testing. A vehicle is a safety-critical device that cannot be tested only using virtual machines. Security testers need to make sure there’s no way to abuse automotive software when it runs on real-life devices. Obtaining the necessary hardware required for final testing can be tricky, however, since it is usually made according to the car manufacturing schedule. To avoid waiting for hardware manufacturers, you can use flexible project management approaches and synchronize testing activities with car production.
Need to swiftly test OTA updates. When a development team pushes a security update, the testing team has to put aside planned tasks and focus on it. They have to ensure that the update fixes the discovered vulnerabilities and doesn’t create new ones when launched on real-life hardware. That’s a great amount of work that has to be done as quickly as possible. This is why security testing of OTA updates has to be done by a highly flexible team that can easily adapt to new tasks.
Poor development standardization in the supply chain. Car manufacturers work with hundreds of suppliers that develop vehicle hardware and software components. Maintaining consistent standards across the supply chain is almost impossible. Suppliers use languages, operating systems, open-source components, and hardware parts that allow them to deliver their products in time and at the lowest possible cost. This creates additional pressure on the security testing team, who has to conduct extensive integration and compatibility testing to search for vulnerabilities in third-party code.
High level of required test coverage. Test coverage usually isn’t a particularly important metric, but it is for automotive software. Test coverage shows the percentage of code covered with tests and the percentage of requirements that aren’t implemented in code. Both parameters can indicate potential security vulnerabilities. Test coverage also helps the QA team identify useless test cases and learn from them. However, achieving a high level of test coverage requires a lot of time-consuming manual work from the testing team, since there are few automated security testing tools for automotive to measure coverage. Manual coverage evaluation also leaves room for human error.
Conclusion
Automotive software makes vehicles safer, more comfortable, and more manageable. Unfortunately, it also makes them a target for hacking. Malicious actors can abuse a car’s software to obtain personal data, steal or damage a vehicle, or harm the manufacturer’s servers.
Thorough automotive cybersecurity testing helps you detect vulnerabilities before hackers can. In the automotive industry, software security testing has to be conducted by a QA team with deep expertise and understanding of the industry, as there are too many unique requirements, best practices, and challenges to take into account.
Security testing teams at Apriorit have vast experience working in many industries, with many technologies, and with unusual requirements. Contact us to discuss how we can help you enhance the security of your automotive software!