Elite cybersecurity engineering for your business
Can’t find the cybersecurity talent you need?
Apriorit is your shortcut to serious engineering power. We help tech leaders secure complex systems, stay ahead of emerging threats, and meet compliance requirements with confidence. Our team brings the unique expertise you need to deliver custom-built protection that perfectly fits your architecture, workflows, and industry standards.
With 20+ years of experience in cybersecurity, we know how to engineer resilient, high-performance solutions across every layer of your technology stack, from kernel to cloud.
Apriorit’s cybersecurity development services give you:
- Fast access to a dedicated team of elite cybersecurity engineers
- Secure SDLC and built-in compliance from day one
- Proactive, future-ready security posture
- Actionable insights from expert-level security audits and pentesting
- Security-focused tech stack tailored to your needs
- Deep expertise in low-level development, data protection, reverse engineering, and advanced threat defense
Full range of cybersecurity development services
Cybersecurity engineering
From small features to standalone solutions, we design custom cybersecurity software tailored to your business’s requirements and workflows.
Partner with Apriorit to tackle unique cybersecurity challenges and cut your software’s time to market.
System programming
Get the low-level engineering power your product needs to be stable, fast, and secure. Delegate your system programming tasks to top-tier cybersecurity experts.

Security testing & audit
Know where your product security stands and what to improve before it’s too late. Get the exact assistance you need, from actionable insights through expert audits, threat modeling, and security testing to implementation of necessary improvements by our engineers.
- Security testing
- Code audit
- Penetration testing
- Vulnerability scanning
- Threat modeling
- Dependency analysis
- Zero-day vulnerability research and exploit development
- Security requirements management

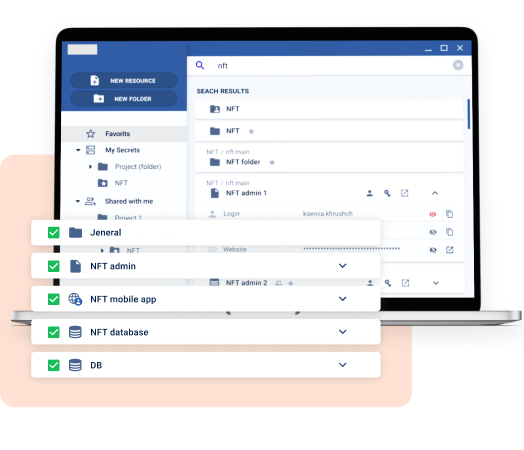
Data protection
Maintain full control and visibility over your most valuable digital assets. Incorporate advanced data protection measures and innovative approaches to secure your data, communications, IP, and trade secrets.
- Data encryption
- Post-quantum cryptography
- Secrets management
- Smart file formats with embedded security
- Clipboard and Office protection
- Email, chat, and web security
- Data loss prevention
- Data backup and disaster recovery
- Cloud and virtual storage protection
Network management
Protect every connection with the right tools and approaches. Design and deploy custom-built network solutions to control access, prevent breaches, and secure your traffic flows.
- Remote access protection
- Secure remote access
- User identification and authentication
- Logging and monitoring
- Software-defined networking solutions
- Remote browser isolation solutions

Blockchain audit
Validate your blockchain product before it hits the market. Whether you need to prove your product’s security to users or gain the trust of investors, you can do it with an audit report from Apriorit experts.
During an audit, our blockchain specialists look for potential vulnerabilities in smart contracts, protocols, and architectures — and give you a clear, prioritized roadmap for fixing them.

Reverse engineering
Gain full visibility and control over your codebase.
Leverage Apriorit’s unique software reversing and research expertise to recover lost documentation, ensure compatibility of legacy systems and third-party components, and introduce advanced cybersecurity measures to your product.
- Vulnerability research
- Malware research
- Threat assessment
- Intellectual property protection

Cybersecurity consulting
When in doubt, consult an expert.
Apriorit will provide you with the insights you need to confidently make strategic decisions at every stage of your project.
We can help audit your current processes and architecture and deliver a clear, prioritized roadmap showing you exactly what to fix and how.
And if you need hands-on help implementing these changes to your project, Apriorit engineers are ready to assist.

Does your business have cybersecurity needs not on this list?
Let’s discuss how we can meet them.
Software-enabled protection for your most valuable assets
Apriorit builds custom security features and systems to protect exactly what your business depends on.
Endpoints
Operating systems
Networks
APIs
Web applications
Mobile applications
Data
Devices
Processes
Firmware
IoT systems
Infrastructure
Chats
Emails
Cloud systems
IndustrY-fOCUSEDcybersecurity services
The industry you operate in dictates your regulatory requirements and technical constraints — and, as a result, how you build your software.
With over 650 projects delivered across 15+ industries, Apriorit experts know how to engineer software with compliance needs and market competition in mind.
Advanced security builtinto every stage of your SDLC
Enhance every stage of your software development lifecycle with extra cybersecurity measures to identify and address vulnerabilities before they turn into problems.
Over the years, we’ve rebuilt our cybersecurity research and development processes to fully adhere to secure SDLC principles:
Guided by leading security standards
As an ISO 27001-certified cybersecurity development company with deep expertise across leading security frameworks, we ensure your solution meets the security expectations of your industry, clients, and regulators.
By delegating your software engineering to Apriorit, you get a cybersecurity development partner who knows how to:
- Protect sensitive IP with strict access controls and encryption
- Harden infrastructure with continuous monitoring and regular audits
- Secure every layer, from project environments to communication channels
- Deliver solutions ready for compliance reviews and stakeholder scrutiny
Want to build your software with other cybersecurity requirements in mind?
Discuss how to implement your specific security requirements with Apriorit experts.
Why trust Apriorit
We have a unique cybersecurity background, extensive domain knowledge, and a rich history of successfully delivered projects.
Clutch
rating
4.9
What you getfrom partnering with us
Full-cycle R&D services
Get expert assistance with everything you need in one place, from concept to deployment to post-launch maintenance.
Proven track record
Enhance your project with an expert engineering team whose portfolio is 70% cybersecurity-related projects.
Top industry expertise
Leverage Apriorit’s insights from top industry events to stay ahead of trends and enhance your product’s security.
Our clients’success stories
Trusted by tech leaders worldwide
Our development workflow
01
Project discovery
We turn your vision into a clear roadmap. By aligning with your goals, analyzing feasibility, and identifying key challenges and risks, we lay a solid foundation for a successful project with no surprises down the road.
02
Technical specification
We craft a detailed technical specification that connects your business objectives with the most suitable technical solutions, ensuring you get a system that’s not only functional but truly fit for purpose.
03
Project estimation
Based on the specification, we define a realistic timeline and design a transparent budget, helping you choose the most efficient cooperation model considering your project’s complexity and priorities.
04
Development and QA
We bring your product to life with a development process focused on reliability, performance, and security, ensuring the final solution meets the highest quality standards and is ready for real-world use.
05
Delivery
After thorough testing, we showcase the completed solution for your approval. You receive everything needed for future scaling and maintenance: the codebase, technical documentation, and a production-ready build.
Engagement models we offer
Benefit from our flexible and transparent collaboration.
Form exactly the team you need right now. Adjust your team or switch between engagement models as your cybersecurity project evolves.
Full-fledged R&D team for your project
Build and customize an all-around self-sustaining team with the full set of specialists your business needs right now.
Team extension for niche expertise
Enhance your in-house development team with Apriorit experts. Swiftly onboard top-tier professionals to fill skill gaps or tackle unique tasks.
Staff augmentation for specific tech expertise
Elevate your team’s capabilities and get access to specialized professionals precisely matched to your project’s unique technical requirements.
FAQ
What are the benefits of outsourcing cybersecurity development?
<p>Your business may get several key benefits from outsourcing:</p>
<ul class=apriorit-list-markers>
<li>Fast access to top-tier cybersecurity talent without hiring delays or overhead</li>
<li>Balanced internal resources</li>
<li>Accelerated time to market</li>
</ul>
With the right partner, you gain specialized knowledge, increased flexibility, and a secure, scalable solution built around your unique needs. All this allows you to focus on your business without worrying about the technical side of your project.
Can you help me ensure compliance with industry-specific requirements?
<p>Yes. Apriorit has experience building solutions that meet a wide range of legal and regulatory requirements, including the requirements of GDPR, HIPAA, NIST , PCI DSS, and DORA.</p>
We follow an internal compliance checklist and embed compliance into our development process so your product is audit-ready by design.
What should I look for when choosing a cybersecurity software development company?
<p>Look for a reliable partner who can offer the right mix of technical expertise, industry knowledge, and flexibility for your project.</p>
<p>Specifically, see if a company has a proven track record and a strong portfolio in cybersecurity software development, preferably with projects similar to yours.</p>
Make sure the team can work with the technologies and tools that are vital for your project. Also, check for relevant industry certifications and positive feedback from previous clients to see if the team is competent, trustworthy, and easy to work with.
How can I effectively assess and improve my product’s security posture?
<p>Start with a full security audit, including risk assessments, penetration testing, and regulatory compliance checks. Follow that with continuous monitoring, incident response planning, and proactive policy updates.</p>
To make sure that you cover all attack surfaces and implement the right changes to keep your product well-protected, partner with a security-focused engineering team like Apriorit.
I’m not happy with my current cybersecurity solution. How can you help?
<p>If your current tools don’t meet your business needs, we will help you identify what’s missing and suggest the most efficient way to close the gaps.</p>
Whether that requires adding a few extra features to your current cybersecurity solution or replacing it with a new custom-made product, Apriorit has the skills and expertise to help you.
Tech insights
and expert tips
-
AI Agents for Incident Response: Use Cases, Autonomy Levels, and Implementation Requirements
A practical guide to designing AI agents for incident response: where they fit, what tasks they can automate, and where humans should stay in the loop…
-
PQC Testing: Why Post-Quantum Needs a Special Security Testing Approach (+ Practical Examples)
Discover key reasons to launch dedicated PQC testing and learn the main attack vectors. Explore practical test examples to fortify your PQC defenses.
-
How to Build a Secure Crypto Wallet with Rust: A Practical Guide from Blockchain Experts
Learn how to build a secure crypto wallet in Rust. Compare Tauri vs Electron, explore Rust’s security benefits, and follow a practical Bitcoin walle…
-
Malware Sandbox Evasion Techniques and Anti-Sandbox Evasion Solutions
Malware sandbox evasion: Discover key and advanced sandbox evasion techniques and best anti-sandbox evasion practices.