How to Detect Vulnerabilities in Software When No Source Code Is Available
In this article, we share our experience in dynamic fuzzing to identify security bugs in such popular image viewers as ACDSee, FastStone Image Viewer...

In this article, we share our experience in dynamic fuzzing to identify security bugs in such popular image viewers as ACDSee, FastStone Image Viewer...

This article is about discovering vulnerabilities even in closed source software by applying fuzzing testing.

This article covers the implementation of forensic features in SIEM solutions and the key requirements to ensure admissibility of data in court.
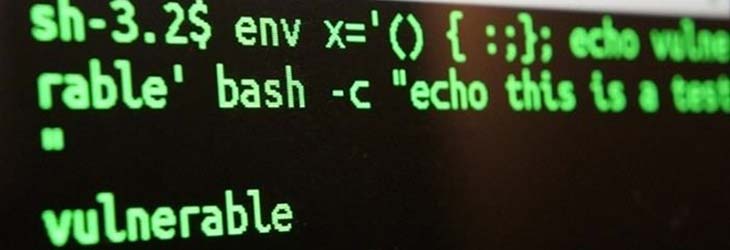
Learn how to protect your application from ever popular stack overflow exploits

A short intro lesson for software reverse engineers considering classes restoration in Delphi. Learn how to get class methods and arguments.

This article is devoted to the implementation of a plugin for OllyDbg debugger to deal with debug blocking using function execution time

White paper to briefly describe nanomite technology for code protection and anti-debug protection with Debug Blocker for Windows applications.
This article is the brief description of the tools and methods, which are used for application architecture research

This article describes the protocol of data exchange that is the modification of the well-known OBEX protocol used in the GSM Samsung phones from the...

How can you recognize C++ FOR operator in Assembler code? See this reverse engineering example.
Tell us about
your project
...And our team will:
Do not have any specific task for us in mind but our skills seem interesting? Get a quick Apriorit intro to better understand our team capabilities.