Power your
business with
Apriorit is a full-cycle software development company that brings niche technical expertise and a security-first approach to every stage of development, giving you exceptional, high-quality solutions from kernel to cloud.
Download Company Presentation (1,4 Mb)Fluent in your
software’s technologies
Why trust
Apriorit?
Working with us, you get a reliable partner for building industry-leading products.
Want to fill in this cell with your success story?
Clients
praise us for
01
Transparent collaboration
Enabling long-term partnerships built on trust, for over 20 years
02
Mature delivery process
Ensuring granular planning, efficient communication, and predictable outcomes
03
Focus on business goals
Enhancing your project with the best fitting skills and technologies
04
Secure SDLC
Prioritizing your software’s security at every step of the way
05
Flexible collaboration
Several partnership schemes for you to choose from
06
Quick onboarding
Enhancing your team with the right experts from our talent pool
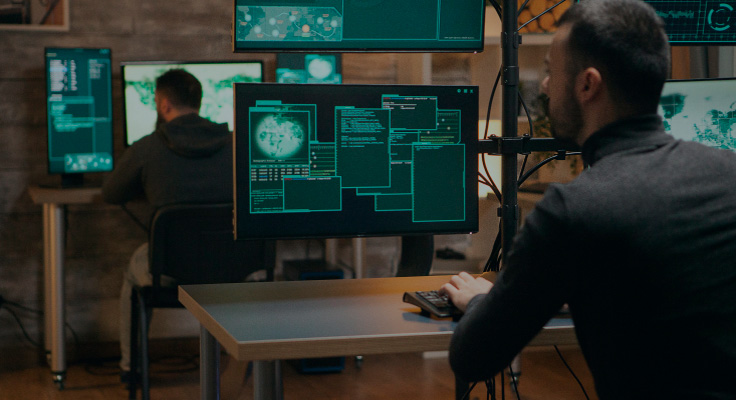
Security-first
approach to everything
Full-cycle software development with security being the center of every stage of your software’s lifecycle.
Guided by industry
standards in cybersecurity
ISO 27001
NIST SP 800-53

TISAX

GDPR
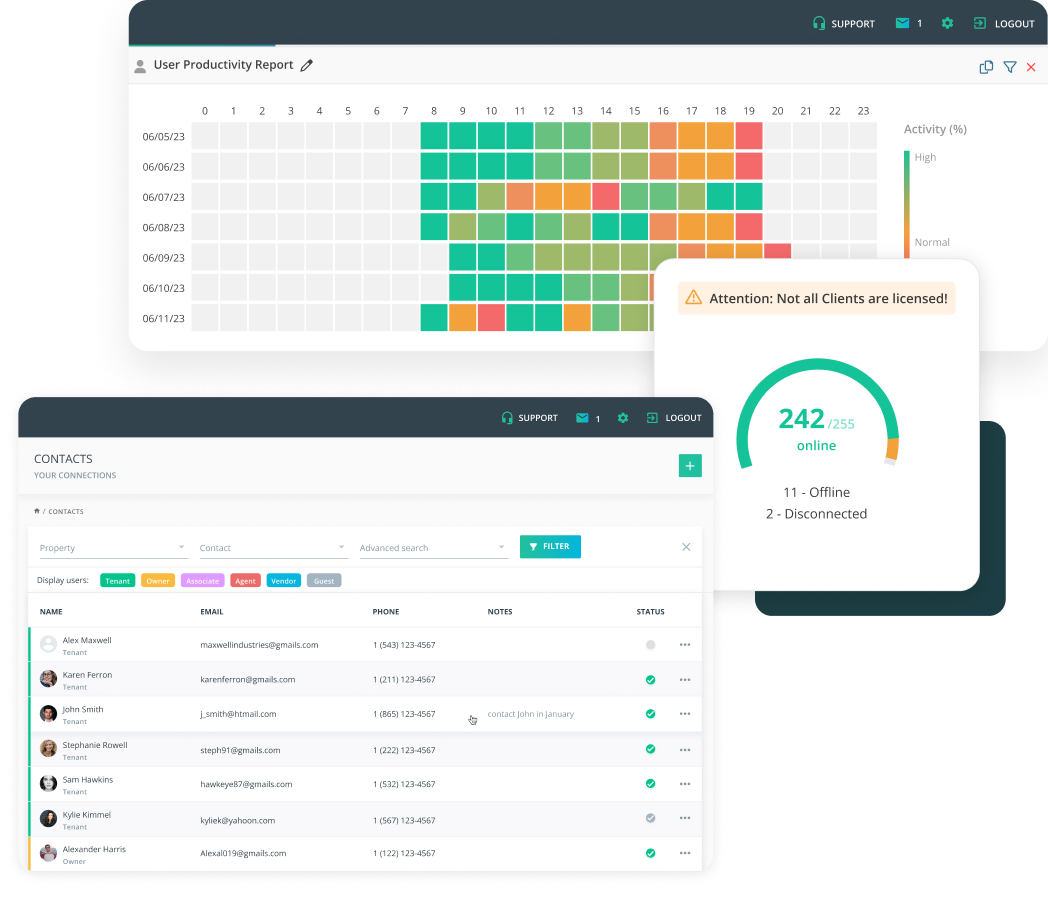
Our clients’
success stories
Industries we serve
and innovate In
From feature integration to custom software development from scratch, Apriorit delivers resilient and industry-tailored solutions that outperform the competition.
Trusted by tech
leaders worldwide
Tech insights
and expert tips
-
Comparing Open Banking API Management Platforms: Apigee vs AWS vs Azure
Choose the right open banking API management platform — AWS, Azure, or Apigee — to make your FinTech product secure, compliant, and scalable.
-
AI for Demand Forecasting: Benefits, Use Cases, and Implementation Tips
AI for demand forecasting: Explore business benefits, use cases, and Apriorit’s tips on how to create effective AI-based solutions.
-
How to Develop a Virtual Disk Driver for Windows: A Practical Example
Learn how to develop a virtual disk driver for Windows that ensures secure data storage, seamless integration, and high system performance.