Key takeaways:
- Before partnering with a software reverse engineering vendor, examine clients’ feedback on their work, cybersecurity principles they apply, as well as their technical experience and approach to project scoping.
- An experienced reverse engineering vendor will provide you with a range estimate, a list of project risks and uncertainties, and a framework for implementation.
- Discoveries made during the research stage can significantly change the project’s scope and difficulty.
- A mature reversing vendor warns clients of potential project risks and discusses how they can avoid or address them.
Reverse engineering demands a completely different skill set than software development. It’s investigative work that requires deep systems knowledge, specialized tools, and the ability to draw accurate conclusions from incomplete information.
Handling reverse engineering in-house often leads to prolonged timelines and unreliable results. But outsourcing reverse engineering raises its own concerns like compliance gaps and security exposure.
In this article, we explain how to outsource reverse engineering without those risks by choosing a reliable reverse engineering partner and preparing effectively for the outsourcing process. Drawing on more than 20 years of experience in low‑level research and cybersecurity analysis, we share practical guidance for technical leaders seeking niche reversing experts.
Contents:
- What to look for in a reverse engineering vendor
- Legal and ethical boundaries of outsourcing reversing tasks
- Outsourcing software reverse engineering: The Apriorit way
- 1. Project intake
- 2. Project discovery
- 3. Initial project estimation
- 4. In-depth analysis and re-estimation
- 5. Milestone-driven execution
- 6. Delivery
- 7. Handover and maintenance
- How to prepare for outsourcing reverse engineering to Apriorit
What to look for in a reverse engineering vendor
Picking a vendor for software reverse engineering differs from picking an outsourcing provider for typical development activities.
When outsourcing traditional software development, you can check whether a potential vendor has experience with projects similar to yours, outsource a couple of small tasks to them, and build your partnership from there.
When it comes to reverse engineering, validating a vendor’s experience becomes challenging, as most delivered projects are protected with NDAs and intellectual property claims. On top of that, you may not have any small reversing tasks that you can outsource to validate the vendor’s competence.
So, how can you assess an outsourcing reverse engineering company?
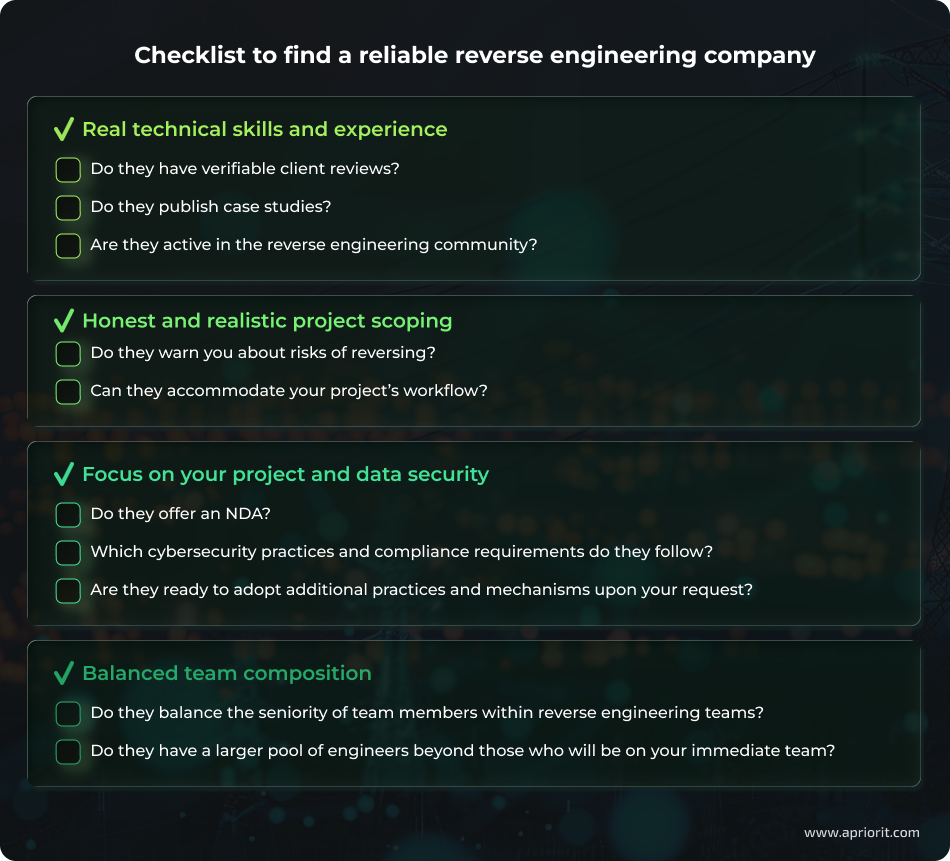
Real technical skills and experience. A vendor with genuine depth in the reversing field will produce content that demonstrates their expertise. When vetting potential service providers, look for sanitized or anonymized project case studies. For example, Apriorit publishes case studies that omit details protected by NDAs but show what we have done for clients and how they have benefited from our reversing expertise.
Another way to confirm a vendor’s experience is to look for real feedback on their work, preferably on platforms like Clutch.co that interview clients directly and publish only validated reviews.
Honest and realistic project scoping. Unlike typical software development, where you can build a clear roadmap, reverse engineering is like searching for a black cat in a dark room. While the task is feasible, each reverse engineering request is unique and can be challenging to estimate even for a skilled team. A trustworthy partner will warn you about this.
We use our hands‑on experience to estimate the scope and complexity of reverse engineering projects. Because we’ve worked on such a wide range of cases, we’re used to identifying risks early, navigating unexpected findings, and communicating those openly with the client.
In well‑defined cases, we can estimate a realistic timeline and budget upfront or structure the work around clear milestones based on our experience. However, reverse engineering projects are research-oriented, so most are handled on a time-and-materials basis. This flexible model allows clients to pay only for the actual effort involved while staying fully informed and in control throughout the process.
Michael Teslia,
Program Manager at Apriorit
Focus on your project and data security. A skilled reverse engineering team prioritizes security. To check a vendor’s approach to security, see whether they:
- Offer to sign an NDA before discussing your project in detail
- Apply cybersecurity best practices (access and identity management, data encryption, data storage, and management protection) in day-to-day operations
- Comply with acknowledged cybersecurity standards like ISO/IEC 27001
- Agree to implement additional cybersecurity measures at your request
Balanced team composition. While reverse engineering requires highly skilled specialists, not all projects will benefit from a team that only has senior reversers. A responsible vendor understands that and can offer you a team that contains:
- Specialists with different seniority levels
- Engineers with skill sets that match your specific task
- Additional specialists in development, QA, project management, etc.
Such a vendor can help you not only reverse engineer software but also interpret results within one team.
Another way to check a vendor’s reputation is by examining how they approach the legality of reverse engineering. We examine key legal and ethical constraints in the next section.
Looking for a reverse engineering team that checks all your boxes?
Reach out to Apriorit and start reversing now!
Legal and ethical boundaries of outsourcing reversing tasks
There are many rules and restrictions around software reverse engineering, but they all boil down to one principle:
You can research, analyze, and build integrations with any legally obtained software or abandonware that doesn’t explicitly forbid it.
For this reason, reputable reverse engineering vendors usually verify that a project request complies with applicable laws and contractual obligations before starting work.
In particular, in Apriorit’s practice, we assess potential risks across several legal areas:
Table 1. Legal constraints for reverse engineering
| Legal area | Core constraint | When reversing is allowed |
|---|---|---|
| Copyright | Copying or reproducing code (temporary or permanent) is typically a restricted act. | – Fair use in the U.S. (e.g., for interoperability or security research) – EU Software Directive (Art. 5 & 6): exceptions for error correction, backup, and interoperability – DMCA exemptions (renewed every 3 years) for security testing, research, and device repair |
| Trade secrets | Illegally acquiring secrets (e.g., via hacking or breach of NDA) is prohibited. | – The product is legitimately obtained, and no contract forbids reversing it. – “Independent discovery” is a full defense. |
| Contracts / EULAs | Many EULAs ban decompiling, disassembling, or reverse engineering. | – Clauses may be unenforceable if they conflict with statutory rights (e.g., EU interoperability rights). – Some jurisdictions restrict unfair contract terms, especially for consumers. |
| International IP | Countries must protect software as literary works and follow global norms. | – Countries may create exceptions if they meet the three‑step test (special case, no harm to normal exploitation, no unreasonable prejudice). |
Breaching these constraints may lead to financial penalties, lawsuits, and reputational losses both for the reverse engineering vendor and their client.
For example, we at Apriorit can involve our legal team into assessment of reverse engineering requests. Once legal clearance is confirmed, our team starts planning the technical work. Let’s look at what this process involves in the next section.
Read also
How to Reverse Engineer Windows Software the Right Way: A Practical Example
Follow a clear, expert‑led process for Windows reverse engineering and avoid the usual trial‑and‑error pitfalls.

Outsourcing software reverse engineering: The Apriorit way
Reverse engineering is at the heart of Apriorit’s expertise, backed by a mature workflow refined through more than 100 successful projects.
We keep this workflow flexible, adjusting it depending on the specific task and our starting point. But generally, we follow this process:
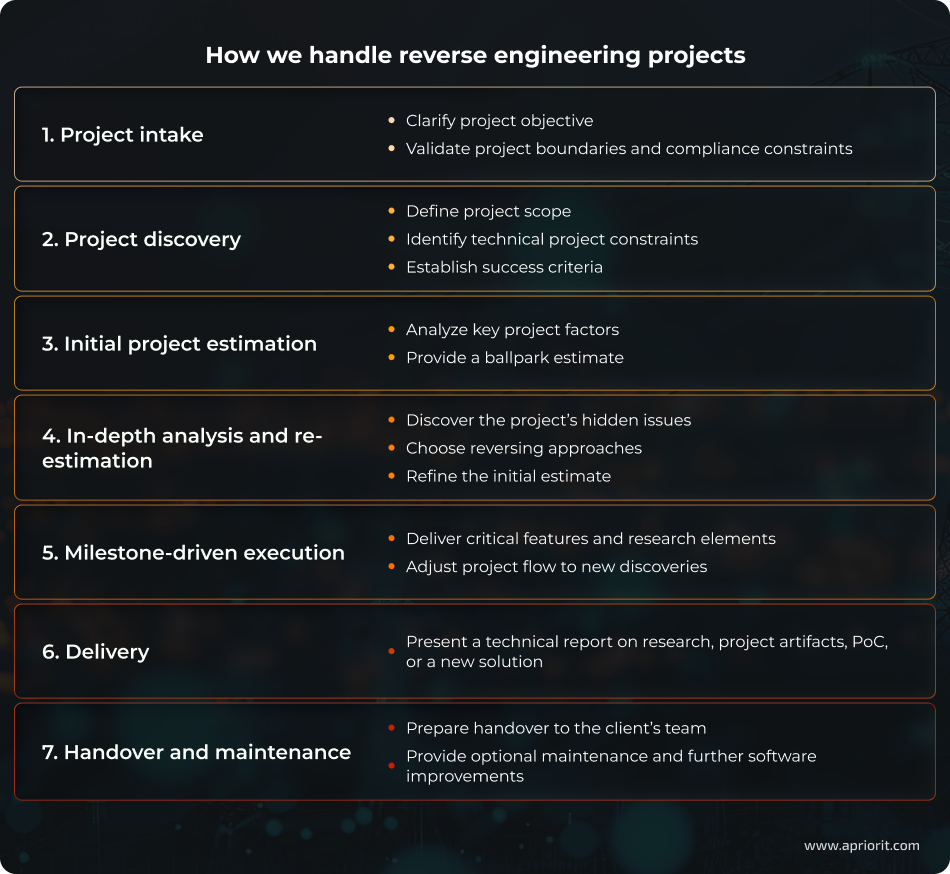
1. Project intake
Every engagement begins with a focused intake phase where we clarify core objectives of the reverse engineering task. This may involve reconstructing protocols, analyzing the root cause of crashes, researching vulnerabilities, and other activities.
At this stage, we also verify all legal, compliance, and permission boundaries to ensure the requested work aligns with relevant regulations and licensing conditions. This includes confirming ownership or access rights and evaluating any contractual and legal restrictions.
If this initial project assessment requires sharing sensitive data, we sign an NDA to create a trusted environment for collaboration.
2. Project discovery
In the discovery phase, we work closely with the client to establish a common understanding of the project. We translate the client’s objectives into a project scope and set of constraints, identifying any limitations related to tooling, access, and timelines. We also align on success criteria by agreeing on what “done” looks like for the particular project.
Additionally, at this stage we gather all available inputs such as binaries or firmware images, system and application logs, memory dumps, captured network traffic, and environmental details. If our task is to analyze a vulnerability or understand unexpected software behavior, we also define any steps required to reliably reproduce the issue.
During project discovery, we typically need access to the client’s physical device, virtual environment, or dedicated test setup to ensure full technical visibility.
3. Initial project estimation
After analyzing the key factors that influence project complexity, we can provide a rough estimate for the project or milestone. Our goal is to give the client a realistic sense of the project scope and highlight any uncertainty or risks early on.
Typical estimate drivers:
- Code size and surface area to analyze
- Protection of the target software
- Platform, architecture, and tooling availability
- Availability, quality, and reproducibility of artifacts
- Expected deliverables
On the surface, a lot of reverse engineering tasks may look similar, but in reality, factors like obfuscation, encryption, platform details, and the client’s end goals can completely change the nature of the work.
For instance, we recently had a client ask us to evaluate the security of their source code — a fairly standard request in this field. But once we started digging in, we found that the code had been compiled with Cython, turning Python into a compiled file. That meant automated reversing tools couldn’t make sense of it.
We figured out a manual approach to reconstruct the core Python logic, demonstrated how an attacker could potentially do the same, and then advised the client on a more reliable way to protect their code.
Michael Teslia,
Program Manager at Apriorit
4. In-depth analysis and re-estimation
Because reverse engineering involves a high degree of uncertainty, we often begin with a short, time‑boxed investigation to validate a project’s core assumptions. Our engineers explore the target environment, confirm that artifacts behave as expected, and evaluate whether initial hypotheses are correct.
This technical exploration helps us identify relevant reverse engineering approaches, discover hidden technical issues, and refine the initial estimate if needed.
5. Milestone-driven execution
We execute the project in focused milestones, starting with the highest‑value target, such as a critical feature, a key protocol flow, or a security‑sensitive component. For each milestone, we focus only on what’s necessary to deliver a concrete, meaningful outcome.
After each delivery, we align with the client through demos, reports, or working artifacts. Together, we verify and adjust scope, priorities, deliverables, and estimates if there are unexpected discoveries.
6. Delivery
Deliverables for reverse engineering projects vary widely depending on the initial request. They can include:
- A technical report that details the methodology, findings, limitations, and recommended next steps
- Artifacts such as recovered or reconstructed code fragments, protocol specifications, message formats, state machines, etc. that we researched
- A proof of concept (PoC) proving that our findings are correct
- A production-ready solution built on the results of reverse engineering. For example, when tasked with researching product integration options, the Apriorit team can also implement those integrations, saving the client time that they can spend on interpreting research results and preparing for their own development project.
7. Handover and maintenance
Once the analysis and validation phases are complete, we prepare a comprehensive handover package designed to make the results immediately usable for the client’s team. This includes all PoC assets, reproduction steps, supporting scripts, harnesses, configuration notes, and any other artifacts required to replicate behavior or independently verify findings.
If needed, we also conduct a walkthrough or knowledge transfer session to ensure that the client’s engineers fully understand how the reversed and developed components work, how to run them, and how our reverse engineering insights can be used in your project.
Beyond the initial delivery, we offer optional post‑handover support to help our clients maintain continuity as the target evolves. If new software versions are released, regressions appear, or the project scope expands, our team can provide follow‑up analysis, updates, and integration assistance.
Read also
How Much Does Software Reverse Engineering Cost? Main Price-forming Factors
Prepare for reverse engineering work with clear cost expectations. Explore how project scope, engineering approach, and IP risks shape your budget so you can balance savings, speed, and technical depth from the start.
How to prepare for outsourcing reverse engineering to Apriorit
Reverse engineering can be successful and streamlined only when your vendor has all the input data they need.
After discussing your project and signing an NDA, we will ask for access to the target software, environment, or device. Having the necessary inputs and access permissions is imperative for accurate and meaningful analysis. When a production environment cannot be shared, a staging setup is acceptable as long as it accurately reflects production; otherwise, reversing results may be incomplete. In many cases, providing a copy of the production software is the most efficient option.
After contracts are signed and access is provided, our team immediately gets to work.
Whether you need integration insights, a security assessment, or a path to extending functionality, Apriorit’s reverse engineers uncover the details that matter and turn them into clear, actionable results. You get the understanding you need — and the confidence to move forward.
Entrust us with your reversing tasks!
We’ll provide you with niche skills and knowledge in reversing to help you avoid project risks.
FAQ
When can reverse engineering be helpful for my project?
<p>Reverse engineering is best when you need to:</p>
<ul class=apriorit-list-markers-green>
<li>Extend existing functionality</li>
<li>Recover a product after source code has been lost</li>
<li>Assess a product’s protection from malicious reversing</li>
<li>Analyze a component or system for potential patent or license violations</li>
<li>Understand proprietary logic, undocumented behavior, or integration requirements</li>
<li>Design integrations with legacy and unsupported systems</li>
<li>Analyse binary files</li>
</ul>
<p>However, reverse engineering isn’t always the most cost‑effective solution. In some cases, if a component doesn’t contain unique algorithms or specialized logic, it may be more practical from a business standpoint to rewrite the software or module from scratch. Common or generic components are often faster and cheaper to re‑implement than to reverse engineer in depth.</p>
<p>In those scenarios, you can use reverse engineering to focus on specific parts of the system that contain unique logic or architectural constraints and rebuild the rest.</p>
Why outsource reversing instead of doing it internally?
<p>Reverse engineering requires niche skills and specialized tools, and the workload for reversers is inconsistent. Most teams don’t keep full‑time experts in areas like assembly, firmware, or malware analysis, so building internal capability is expensive and slow.</p>
<p>Specialized external teams bring broader experience, faster turnaround, and tooling already optimized for this type of work. Outsourcing lets companies handle complex or one‑off reversing tasks without maintaining a permanent, highly specialized reverse engineering function in‑house.</p>
How do you handle sensitive data we share during reverse engineering?
<p>We treat all client data as sensitive by default. Only a limited number of specialists involved in the engagement receive access, and all data is exchanged through secure encrypted channels.</p>
<p>Our processes follow GDPR, ISO 27001, NIST SPs principles, including strict access controls, purpose limitation, and secure storage. We work with the minimum amount of information required and isolate it within the project’s secure environment. This ensures sensitive records like PII, proprietary logic, or cryptographic material remain protected throughout the reverse engineering process.</p>
Can you reverse engineer a solution without complete source code or documentation?
<p>Yes. Reverse engineering is often performed with little or no documentation and without access to the original source code. In those situations, the analysis relies on binaries, firmware images, network traffic, system behavior, crash dumps, or any operational traces your team can provide. Apriorit’s engineers can reconstruct architecture, logic, and data flows directly from the compiled artifacts and runtime behavior.</p>
Can you work with a partial project scope?
<p>Yes, we can. For example, we can analyze just one protocol or only conduct a risk assessment. It’s common for clients to work with us on a narrowly defined component or a specific type of analysis.</p>
<p>However, even when the initial scope is limited, some level of broader product understanding is usually required. To properly analyze a protocol, investigate a crash, or assess risk, we often need context about the surrounding architecture, data flows, and how the component interacts with the rest of the system. This additional insight ensures that our findings are accurate and actionable rather than isolated from real product behavior.</p>
Can outsourced reverse engineering happen in parallel with our own in-house development?
<p>Yes. When working as dedicated specialists, our reverse engineers collaborate with your in-house team and adjust our milestones to your development schedule.</p>
<p>Our reversers can also work on a specific part of your solution. For instance, they can reverse engineer a specific protocol or research an integration while your development team works on other tasks.</p>



