Every year, the RSAC Conference gathers people who immerse themselves in cybersecurity. In 2026, 40,000 of them came to San Francisco with the same question on their minds: Now that AI is everywhere, who is actually in control? And the answer is: It’s the community.
This year marked a shift in the industry’s mindset. Previous discussions were centered around we have AI! RSA 2026 made it clear that the focus has matured to now let’s secure it. As AI becomes deeply implemented into products and operations, the conversation shifts from experimentation to control, governance, and real-world risk management.
For Apriorit, this was our fourth year attending the RSAC Conference. Our team joined sessions, panels, and discussions with industry experts to better understand where cybersecurity is heading.
In this article, we share firsthand insights from Apriorit’s team, focusing both on trends and their impact on software security, resilience, and future-readiness.
Contents:
- Key strategic shifts from RSA Conference 2026
- Assume the attacker is already inside
- ‘Good enough security’ becomes a real strategy
- AI reshapes both threats and defenses
- AI systems introduce new security boundaries
- Identity becomes the new perimeter
- Security is consolidating around platforms
- Cloud security can no longer keep up with cloud complexity
- The boardroom now speaks security — in business terms
- People remain at the center of security
- AI governance becomes the next security frontier
- Turn insights into action with Apriorit
Key strategic shifts at RSAC Conference 2026
RSAC Conference 2026 made it clear that attackers have more tools, more patience, and more access than ever before. The industry’s response is a fundamental reset in how security is designed, governed, and operated.
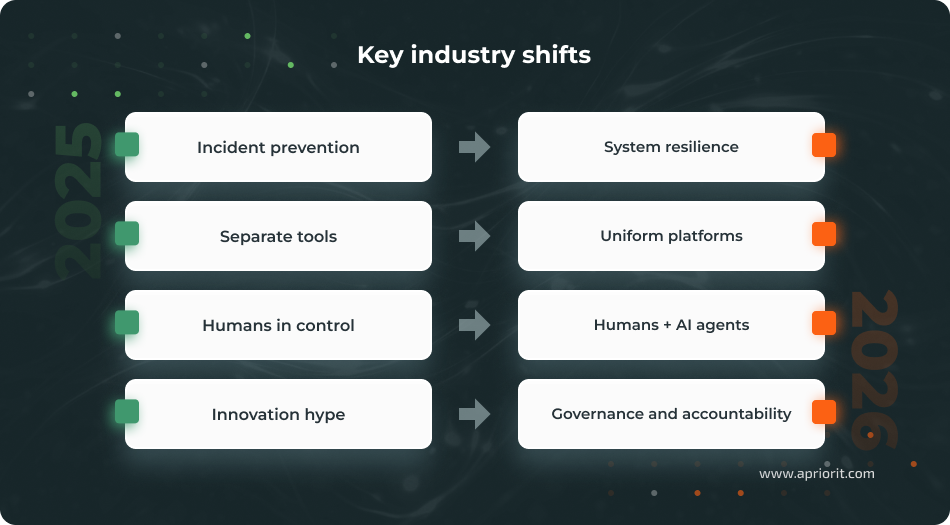
These shifts set the context for everything that follows. Here is what our experts observed during the conference.
Insight 1. Assume the attacker is already inside
A decade ago, cybersecurity was built around events: detect the breach, block the attack. At RSAC 2026, that model was openly challenged. In his panel, Jim Richberg highlighted that nation-state actors increasingly penetrate systems and remain undetected, waiting for the right moment to act.
As Natalia Yurko, Apriorit’s VP of Strategy and Partnerships, puts it:
“Cybersecurity is no longer about building walls. It’s about thinking like the person trying to break them.”
This changes the fundamental logic of security design. If an attacker may already be inside, the question shifts from How do we keep them out? to How quickly can we see them, contain them, and keep operating?
So, detection becomes more important than prevention. For product teams, this means:
- Continuous monitoring as a default instead of an add-on
- Faster response loops to limit damage
- Designing for compromise, not avoidance
Concerned about evolving cyber threats and compliance demands?
Empower your team with Apriorit specialists who deliver a secure SDLC, advanced threat defense, and tailored protection strategies.
Insight 2. “Good enough security” is a real strategy
Another key takeaway from the RSA Cybersecurity Conference 2026 is a more pragmatic approach to security. Instead of striving for perfect protection, organizations are focusing on efficiently reducing real-world risk.
This approach prioritizes:
- Reducing the attack surface
- Focusing on critical risks
- Making systems less attractive targets
- Maintaining compliance without unnecessary complexity
At the leadership level, this means treating security as economic decision-making, weighing trade-offs between speed, cost, and protection, and being able to defend those choices.
Insight 3. AI reshapes both threats and defenses
As discussed at the Cybersecurity in the Boardroom panel led by SecurityScorecard, AI is becoming the environment in which both attackers and defenders operate.
Attackers are already using AI to scale and accelerate their operations, design convincing phishing campaigns, and speed up attack cycles. At the same time, defenders rely on AI for detection, automation, and response.
After the panel, Lidiia Mandrovna, Apriorit’s VP of Innovation and Technology, shared her thoughts:
“AI is an ‘existential rescue’: the risk of not using it is now greater than the risk of adopting it.”
This creates a new reality:
- Smarter and faster attackers
- Less time to detect and respond to threats
- Greater reliance on AI-driven defense
Natalia Yurko, Apriorit’s VP of Strategy and Partnerships, notes that under these conditions, security products must evolve beyond alerting. The focus is shifting toward decision support systems and AI-assisted security operations that can keep up with machine-speed threats.
Insight 4. AI systems introduce new security boundaries
Governing AI-Native Development, a panel hosted by Legit Security with participants including Temi Adebambo, Sean Poris, James Robinson, and Jim Routh, addressed one of the most consequential shifts at this year’s conference: AI is reshaping who and what does the building.
We are moving from human-written code to agent-driven systems, where AI agents build, test, and interact with other agents at machine speed. This shift introduces entirely new risks:
- Shadow agents operating outside visibility
- Uncontrolled autonomy across systems
- Limited understanding of agent behavior
In other RSA Conference 2026 news, a key idea emerging from these discussions is simple: AI must secure AI. Security must move inside the development lifecycle and continuously operate in the background, like an immune system.
Read also
How Big Data and AI Work Together (And What to Do if They Don’t)
Understand how AI and big data can help you uncover hidden patterns, optimize operations, and make data-driven decisions that improve business performance and competitiveness.
Insight 5. Identity is the new perimeter
As cloud environments grow more dynamic and AI agents multiply, the traditional network perimeter loses its meaning. At RSAC 2026, identity emerged as the new boundary, so the conversation has expanded well beyond human users.
Non-human identities now outnumber human identities in the form of:
- Machine accounts and service tokens
- API keys and automated pipelines
- Autonomous AI agents
Yet most organizations still lack the visibility and controls to manage these identities at scale. Olha Kolomoets, Apriorit’s VP of AI Engineering and Integration, highlighted:
“Evolution of identity is the new perimeter, especially managing non-human identities and AI agents with PAM-like controls.”
The implication is clear: Organizations need real-time identity visibility and lifecycle management that covers every entity acting in their systems.
Insight 6. Security is consolidating around platforms
For years, security stacks grew by addition, which meant adopting a new tool for each new threat. As a result, there were dozens of disconnected point solutions, each generating its own alerts and its own blind spots. RSAC 2026 reflected a clear industry response: consolidation.
Platform-based approaches provide:
- Better interoperability between security components
- Centralized visibility and context
- Reduced duplication of data and functionality across tools
- Faster, better-informed decisions
For organizations, this means rethinking how security systems are built and connected. Instead of adding more tools, the focus shifts to integrating existing tools into cohesive platforms, strengthening the overall security of these interconnected environments.
Insight 7. Cloud security can no longer keep up with cloud complexity
Cloud environments were never designed to stay still — and that is precisely what makes them hard to secure. Olha Kolomoets, Apriorit’s VP of AI Engineering and Integration, flagged this as one of the clearest themes from the third day of the 2026 RSAC Conference: Security teams simply do not have full visibility into what is running, where, and how it is connected.
This creates a fundamental challenge: Traditional security approaches designed for static environments no longer keep up with cloud dynamics.
To address this, organizations are shifting toward:
- Real-time asset awareness
- Context-driven security decisions
- Integrated, cloud-native security controls
Without these, it would be challenging to maintain consistent security in modern cloud environments.
Read also
Multi-Cloud Security: Challenges to Consider and How to Secure Multi-Cloud Infrastructure
Understand how to address security gaps in multi-cloud environments by implementing consistent policies, improving visibility, and mitigating risks across all platforms your business relies on.
Insight 8. The boardroom now speaks security — in business terms
The Cybersecurity in the Boardroom panel hosted by SecurityScorecard addressed a shift that has been building for years and has now fully arrived: Security is a board-level conversation, and the language has changed.
Technical metrics no longer carry the room. Boards want to understand business risk: what an incident would cost, how quickly operations could recover, and what investments are actually reducing exposure. Two frameworks are gaining traction:
- Return on mitigation — quantifying how much a security investment actually reduces financial risk
- Security as business enabler — framing security not as a cost center but as the foundation that allows the business to move fast with confidence
The question of Are we secure? has been retired. The question that matters now is How fast can we recover?
This shift also reshapes the CISO role: technical expertise alone is no longer enough. The most effective security leaders today are enterprise strategists, who are able to translate risk into business impact and align security decisions with organizational goals.
Insight 9. People remain at the center of security
The official theme of RSAC 2026 — Power of Community — reflects this. Despite fast automation and AI adoption, collaboration and human connection remain central to cybersecurity.
A focus on real connections is shaping a more collective approach to security:
- Shared responsibility across organizations
- Ecosystem-driven collaboration
- Stronger reliance on partners, vendors, and communities
The most meaningful moments at the conference were not in the keynotes but in the conversations with peers, partners, and practitioners who have shown up year after year and picked up where they left off.
Insight 10. AI governance is the next security frontier
The RSAC Innovation Sandbox offered a clear signal of where the market is heading: every finalist is building with AI. The winner, Geordie Al, built a security and governance platform purpose-built for AI agents. Geordie AI provides enterprises with real-time discovery and visibility across their entire agentic footprint: what agents are running, what they are connected to, and how they are behaving.
This is a strong indicator that the industry is moving beyond experimentation. As AI adoption accelerates, the focus is shifting from building AI systems to controlling and securing them.
In many ways, this marks the end of the Wild West phase of AI adoption. Governance, visibility, and control are becoming essential and will likely play a central role in how organizations approach AI regulation and compliance going forward.
Turn insights into action with Apriorit
RSAC 2026 cybersecurity trends made one thing clear: Cybersecurity is entering a new operational reality. Today, the focus is on operating confidently in environments that are never fully secure.
At Apriorit, we specialize in turning these industry trends into practical solutions.
We help companies:
- Secure AI systems and agent-driven architectures
- Build resilient systems that can withstand real-world threats
- Implement security that works in practice, not just on paper
We base our collaborations on deep technical knowledge and 20+ years of real-world experience, not trends. If you’re looking for a partner who understands where cybersecurity development is going, Apriorit is ready to help.
Security and AI expertise are rarely found together — Apriorit has both.
Our experts create secure, AI-ready software by understanding the latest threats at the engineering level.




