Cybersecurity teams often know how an attack could happen but struggle to explain what it would actually cost. Complex, multi‑stage risks are easy to describe in theory and hard to quantify in terms of real business impact.
That’s why the factor analysis of information risk (FAIR) framework is becoming popular among businesses that work with sensitive data but struggle with assessing and prioritizing security efforts. FAIR turns technical threats into clear, defensible estimates of likelihood and loss, giving leaders a solid basis for making security investment decisions.
Yet the FAIR model is only as effective as the tools that support it.
To build reliable and scalable FAIR workflows, companies need cybersecurity products that can gather the right data, structure it properly, and guide users through consistent, repeatable analysis.
In this article, we break down exactly how FAIR works and which tools and capabilities it requires. This assessment will be helpful for development leaders and project owners who are building cybersecurity tools and want their products to support FAIR implementation.
Contents:
- Why quantitative cyber risk management is critical for modern business security
- What is the FAIR model?
- Using the FAIR model
- Benefits of adopting the FAIR model
- Who uses the FAIR model? Real-life examples
- Implementing the FAIR model for software development: Apriorit’s advice
- Design FAIR-driven cybersecurity tools with Apriorit
Why quantitative cyber risk management is critical for modern business security
As companies grow and handle terabytes of sensitive data, their cybersecurity decisions increasingly affect revenue, potential losses, and long‑term strategy. Business leaders need to understand cyber risk not only in technical terms but also in clear financial terms that support informed decision‑making.
Most traditional risk management approaches, like ISO 27005 or the NIST Risk Management Framework, help organizations identify risks, classify them by impact level, and apply standard security controls. These approaches are valuable for establishing structure and consistency, but they provide only qualitative risk assessments like low, medium, or high. For executive stakeholders, these risk levels don’t answer the most important questions:
- How much financial loss could a specific risk cause?
- Which risks should be prioritized first based on potential business impact?
- How much should the organization invest in security controls?
- How significantly will each control actually reduce financial exposure?
This is where cyber risk quantification (CRQ) becomes essential.
Cyber risk quantification provides tools to convert cyber threats and vulnerabilities into estimated financial impact. This allows you to evaluate potential loss in monetary terms, rank risks by impact, and justify security investments with concrete evidence.
Compared to traditional risk assessment methods, cyber risk quantification gives businesses:

The companies that get the most out of CRQ are usually those with a lot to lose from a cyber attack. They include:
- Banks, insurance companies, and other FinTechs
- Healthcare organizations
- International enterprises
- Energy and utility providers
- Telecommunications providers
- Retailers
Implementing cyber risk quantification requires both organizational effort and investment in security tools. That’s why CRQ adoption is a trend among software development companies that build products for cybersecurity scoring, vulnerability scanning and assessment, or compliance and reporting.
One of the best-known ways to adopt cyber risk quantification is using FAIR — a framework that provides businesses with tools to estimate the impact of security risks in terms of real dollars. Let’s examine this model in the next section.
Overloaded with tools but lacking insights?
Unify your cybersecurity efforts with Apriorit, a partner who connects audits, testing, monitoring, and incident response into one coherent, business-oriented protection strategy.
What is the FAIR model?
FAIR is a quantitative risk assessment methodology that can help you understand, analyze, and measure cybersecurity and operational risk in financial terms. It provides a precise way to assess risk with measurable parameters that show:
- How often particular threats become reality
- How vulnerable assets are to those threats
- How much loss an organization would experience if an event occurred
With this framework, organizations can build different security scenarios, compare the cost‑effectiveness of controls, and make business decisions based on relevant and easy-to-understand data analysis.
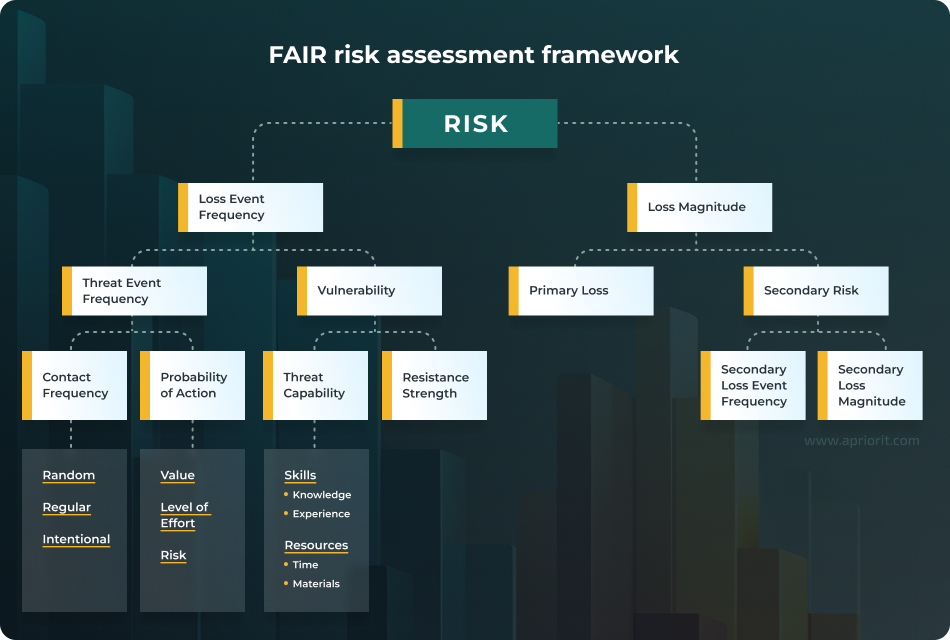
According to FAIR, a risk comes down to two things: how likely a security incident is to happen (Loss Event Frequency) and how costly it would be if it did (Loss Magnitude). Risk is calculated as Risk = Loss Event Frequency × Loss Magnitude. Both loss event frequency and loss magnitude are calculated based on other factors:
Using the FAIR model
Applying the FAIR model for cyber risk assessment helps companies take into account all aspects of cybersecurity risks and their consequences. Let’s see what using this model looks like in a real example.
Say that your company needs a way to assess and prioritize vulnerability fixes in your SaaS product. Using the FAIR model, your team breaks down each vulnerability into measurable components:
Loss Event Frequency: How often could each vulnerability actually be exploited? Estimate Threat Event Frequency (how often attackers might try) and Vulnerability (the likelihood they’d succeed). A critical XSS bug might face low threat activity, while a moderately risky SQL injection in checkout is a prime target.
Loss Magnitude: If exploited, what’s the financial hit? Calculate potential losses — data breach costs, regulatory fines, customer churn, incident response, and downtime.
The result: Multiplying frequency × magnitude reveals that a SQL injection will result in around $2M in annual risk exposure versus $50K for an XSS exploit. Now, your engineering team has a defensible, dollar-based priority list, and your leadership understands exactly what they’re protecting and why the budget matters.
While using the FAIR model is a good way to estimate your cybersecurity risks, it’s important to remember that it isn’t a standardized framework like NIST CSF. FAIR is a complementary model that should be used alongside other risk assessment approaches like ISO/IEC 27002, NIST Risk Management Framework, or TARA. When combined with them, the FAIR model helps you assess and prioritize risks, while other frameworks provide tools for risk discovery, monitoring, and mitigation.
Even as a complementary risk assessment model, FAIR is becoming increasingly popular among large businesses that work with sensitive data and have a lot of cybersecurity regulatory obligations. In the next section, we take a look at key benefits these companies expect to receive from adopting this model.
Benefits of adopting the FAIR model
FAIR is the only internationally recognized model for quantitative cyber and operational risk assessment. Other quantitative approaches like RiskLens, Cyber VaR, or OCTAVE are not as popular, as they are less focused on finances, less structured, or less supported.
Adopting FAIR for risk assessment guarantees an organization the following benefits:

Who uses the FAIR model? Real-life examples
Companies across various industries and of different sizes adopt FAIR to simplify cybersecurity risk assessment. Notable examples include:
- Fidelity Investments. This financial organization relies on FAIR to run an internal risk assessment program, build risk scenarios, pick best-suited cybersecurity measures for those scenarios, and make security estimates understandable for company stakeholders.
- Hewlett-Packard Enterprise (HPE). FAIR helps Hewlett-Packard assess risks and adjust to a rapidly changing security threat landscape. It also helps enterprise leaders put security risks into perspective and communicate information about risks and investments clearly across a diverse and distributed organization.
- NASA. Federal agencies are under a lot of pressure to justify cybersecurity spending and at the same time ensure bulletproof data protection. NASA adopted quantitative risk management with FAIR to reach both goals and improve security risk analysis for its tech operations.
- Netflix. The video streaming service uses FAIR-based risk analysis to prepare data for business decisions on the platform’s cybersecurity. Netflix uses three tiers of FAIR deployment for strategic, tactical, and operational decisions. This system allows Netflix to assess security project costs and compare them to opportunity costs of investing in other priorities.
- Swisscom. Switzerland’s largest telecom provider switched from qualitative to quantitative risk assessment to better prioritize risks. FAIR helps Swisscom prioritize risk mitigation resources and calculate ROI for cybersecurity investments.
When companies like these want to adopt the FAIR model for cybersecurity assessment, they start looking for tools that support it. In the next section, we examine how you can build tools that help implement FAIR.
Read also
Cloud Vulnerability Scanning for Cloud Infrastructure Security (+ Practical Automation Example)
Stop using vulnerability scanning as a checkbox for audits. Turn it into a source of clear, actionable decisions your team can actually follow through on.

Apriorit’s recommendations for implementing the FAIR model for software development
While FAIR implementation doesn’t require dedicated tools, an organization’s existing cybersecurity infrastructure should be able to support the data collection and processing needed for quantitative risk management.
Here are practical tips to successfully enable FAIR support based on our own experience:

1. Establish the risk analysis infrastructure
Supporting FAIR adoption requires a deliberate technical foundation that ensures the model is fueled by reliable, consistent, and decision‑ready data.
To collect that data, identify potential sources and plan for integration. Vulnerability scanners, SIEM logs, and penetration test reports contain signals needed to estimate threat event frequency and vulnerability.
Once sources are defined, develop pipelines that aggregate and standardize threat intelligence data. Automated ingestion workflows help convert raw intelligence into objective metrics that align with the model’s threat event frequency logic. For example, when security analysts can see patterns in attacker behaviors, exploit availability, and campaign frequency, they can clearly estimate the magnitude and frequency of a potential security incident.
To maintain consistency across the ecosystem, define clear data normalization standards. Unlike many risk management frameworks, FAIR doesn’t use Common Vulnerability Scoring System (CVSS) scores. However, many other standardized cybersecurity tools use CVSS.
If you want to use these scores as one of the metrics, implement translation rules that convert raw CVSS values into FAIR‑relevant factors. You can do this by mapping CVSS exploitability metrics to threat capability, or by calibrating severity ratings to reflect the probability that an attempted exploit will succeed.
Establishing these standards ensures consistent risk assessment and allows your FAIR‑powered software to produce transparent and quantitatively defensible risk results.
2. Select tooling and integrations for your DevSecOps workflow
A FAIR‑supportive toolchain works best when it’s connected to continuous, iterative DevSecOps pipelines. When FAIR data flows through the same pipelines that manage code, infrastructure, and security findings, analysts get more security-related data and can continuously quantify risks.
Integrating the FAIR process into existing DevSecOps pipelines starts at the design phase.
Connect threat modeling outputs like identified threat events, assets, and attack vectors directly into your FAIR analysis templates. This ensures that architectural risks discovered early in development immediately become quantifiable scenarios.
Similarly, link vulnerability management platforms to get access to data that influences threat event frequency and control strength. This might include defect trends, exploitability indicators, scan results, or metadata about system exposure. Automated data ingestion saves analysts effort on data gathering and helps maintain up‑to‑date assessments as systems evolve.
Finally, integrate FAIR outputs with popular ticketing or work tracking systems. By treating each quantified risk scenario as a tracked item, analysts can monitor progress, prioritize based on potential loss exposure, and maintain a clear audit trail. This closes the loop between identifying risk, quantifying it, and driving remediation within the same workflow that DevSecOps teams already rely on.
Read also
Anomaly Detection in Cybersecurity: Techniques, Challenges, and Development Best Practices
Strengthen your cybersecurity framework with expert insights on anomaly detection. Learn to spot irregular patterns, reduce risks, and protect critical assets — with relevant technologies.

3. Create analysis templates and playbooks
To make FAIR usable in day‑to‑day security work, your security analysts require clear, repeatable templates.
A proven first step to implement them is to define a small set of standard risk scenarios that companies working with sensitive data often face: supply chain attacks, data exposure risks, service availability issues, code integrity problems, and so on. Having these scenarios documented helps analysts start from the same point and keep their analysis results consistent and comparable.
Next, build pre‑filled FAIR analysis templates for each scenario. These should outline the typical assets involved, likely threat actors, common ways for a scenario to unfold, and the usual types of impact. By giving analysts a head start, templates speed up the process and make the results more consistent.
4. Prepare data for reporting
Preparing data for reporting is just as important as analyzing it. For convincing and easy-to-understand reports, analysts need visualizations that clearly illustrate risk distributions, including curves that show the probability of different loss magnitudes. These visuals help decisions-makers understand uncertainty and compare scenarios without needing deep statistical expertise.
To enable such reporting, add finance-focused dashboards that automatically translate technical risk data into financial terms. Key elements include annualized loss expectancy for each scenario and side‑by‑side comparisons of these values with the cost of proposed controls.
Additionally, your tools can generate prioritization matrices that rank vulnerabilities and risks by quantified business impact rather than technical severity alone. By aligning vulnerability data, asset value, and modeled loss impact, these matrices highlight the risks that matter most to the business.
As you can see, building a security tool that supports FAIR analysis requires a development team that combines data management, DevOps, security testing, data visualization, and other skills. Building such a team internally can take a lot of time and resources. Many companies prefer to outsource some or all associated development tasks to a vendor like Apriorit and spend the resources they save on other business goals.
Design FAIR-driven cybersecurity tools with Apriorit
As a company dedicated to building custom cybersecurity software, Apriorit provides all the services you need to build a FAIR-supportive tool. We have real experience in end-to-end development of cybersecurity platforms, enhancing existing cybersecurity tools with new features, and modernizing legacy security solutions.
Our clients especially value these Apriorit services:
Cybersecurity software development and consulting. Apriorit unites niche cybersecurity development expertise, including specialists in kernel-level development, with mature delivery processes and no-nonsense communication. We’ll help you build exactly the tool you envision, or consult on the most challenging aspects of the process.
Big data development. Risk assessment can only be as good as the data on which it’s based. Apriorit will help you build reliable pipelines to collect raw data, process it, and store it in standardized and optimized databases.
API integration. Choose the products and system you want your tool to integrate with and we’ll ensure secure, performant, and seamless connections. In some cases, we apply ethical reverse engineering to integrate with closed or legacy platforms for which documentation isn’t available.
Security testing. Testing is the best way to gather information about the real state of a company’s cybersecurity posture and existing vulnerabilities. To help you get the complete picture, we can conduct penetration testing, test compliance and incident threat response, and audit your code security.
DevSecOps pipeline design and development. We design and implement DevSecOps pipelines that automate security checks at every stage of CI/CD. Our team integrates code scanning, dependency checks, configuration validation, and other essential controls into a streamlined workflow. As a result, you get a unified, scalable, and automated pipeline for data processing and cybersecurity tasks.
Need to adjust your tools to support FAIR?
Let’s discuss how Apriorit teams can help you customize your tools or build new solutions for risk assessment!
How does the FAIR framework differ from traditional risk assessment methods?
<p>FAIR takes a quantitative approach, while most traditional methods rely on qualitative scoring such as high/medium/low risk impact. Instead of providing subjective heatmaps, FAIR models how often loss events are likely to occur and how much they may cost the business financially.</p>
<p>This shift from categorical ratings to financial estimates makes risk comparisons more objective, easier to visualize, and defensible during decision‑making.</p>
What types of organizations benefit most from FAIR-based risk quantification?
<p>Regulated industries such as finance, healthcare, and insurance extensively use FAIR. However, the FAIR model isn’t created with a specific industry or type of organization in mind. Any company that needs to justify cybersecurity spending, prioritize security risks, or demonstrate measurable risk reduction can benefit from adopting FAIR.</p>
Does FAIR replace frameworks like NIST or ISO 27005?
<p>FAIR complements frameworks such as NIST CSF, NIST 800‑53, ISO 27001/27005, and SOC 2. It adds a quantitative layer to their existing control‑based approaches but doesn’t provide tools to detect and manage risks independently.</p>
<p>Many organizations combine governance and control mechanisms from NIST or ISO with the FAIR model’s approach to risk analysis and prioritization. This way, they get proven ways to stay on top of cybersecurity vulnerabilities and assign dollar values to discovered risks.</p>
How does FAIR help justify cybersecurity investments to business stakeholders?
<p>FAIR helps estimate the impact of a potential risk and the investment needed to prevent it in terms of dollars. Instead of saying a control is important “because it reduces risk,” teams can show how a proposed investment reduces expected annual loss.</p>
<p>This gives company stakeholders a clear basis for comparing cybersecurity initiatives to other business priorities and making budget decisions grounded in ROI.</p>
What data is required to perform FAIR risk analysis?
<p>A FAIR assessment typically requires:</p>
<ul class=apriorit-list-markers-green>
<li>Incident and event history — past security incidents, outage reports, fraud cases, and near‑miss data that show how often specific events occur</li>
<li>Operational security metrics — vulnerability scan results, patch timelines, authentication logs, monitoring coverage, and control performance metrics</li>
<li>Threat intelligence and SOC data — indicators of compromise, attack patterns, and industry reports</li>
<li>Business impact and financial data — cost of downtime per hour, labor rates for response and recovery, third‑party service costs, regulatory penalties, and customer impact metrics</li>
<li>Asset and data inventories — system criticality ratings, data classification levels, record counts, transaction volumes, and architectural exposure (e.g., internet-facing vs. internal)</li>
</ul>
Can FAIR be integrated into secure SDLC and DevSecOps workflows?
<p>Yes. FAIR integrates well with both secure SDLC and DevSecOps because it uses data that engineering and security teams already generate throughout the development lifecycle.</p>
<p>In most organizations, the information needed for FAIR (vulnerability trends, defect density, remediation times, threat‑model outputs, incident history, system inventories) is already collected as part of secure SDLC practices. FAIR adds a quantitative layer on top of this data, helping teams evaluate which design flaws, security gaps, or technical debt create the largest financial exposure.</p>
<p>In DevSecOps environments, the same operational data streams — CI/CD security scan results, backlog analytics, log and monitoring data, and performance of security controls — feed directly into FAIR models.</p>
How does FAIR support prioritizing cybersecurity risks and remediation efforts?
<p>By quantifying loss exposure, FAIR highlights which risks drive the largest expected losses. This gives security and engineering leaders a data‑driven way to sequence remediation work, evaluate alternative mitigation strategies, and show measurable progress over time. FAIR reduces the debate around “critical vs. high” labels and centers the conversation on business impact.</p>
What tools are commonly used for FAIR-based cyber risk quantification?
<p>Organizations usually combine FAIR platforms with their own tooling. Commercial solutions like X‑Analytics and Safe Security offer built‑in FAIR models, Monte Carlo simulations, and reporting.</p>
<p>Teams that use custom or adapted solutions often build them with FAIR requirements in mind, designing data collection pipelines, creating dedicated reporting, and adding FAIR calculation modules that pull data from vulnerability management, CI/CD pipelines, or asset inventories. This lets them embed FAIR into existing workflows instead of replacing current systems.</p>




