
Alina
Market Research Specialist
As part of the Apriorit team, I aim at providing firsthand insights on tech and business, focusing on the true value of technologies and concepts and discussing pros and cons of applying them in IT projects.
More articles from author
Cybersecurity Risks of Automotive OTA Updates and How to Mitigate Them
Discover key risks for vehicles' OTA (over-the-air) cybersecurity and precent them with Apriorit’s proven development practices.

How to Detect Banking Fraud Using Machine Learning
Explore the key reasons and use cases for using machine learning for fraud detection in banking, as well as expert tips on building a custom system.

The Why and How of Creating a Digital Wallet
We walk you through how to create a digital wallet step by step and discuss wallet types, must-have features, and business benefits.

Developing a Warehouse Drone Management System: Architecture, Key Features, Technology Stack
Explore Apriorit’s overview of warehouse drone management system development, from use cases and features to app architecture and tech stack.

10 Best Practices to Ensure Embedded System Security
Explore the key risks to embedded system security, the attacks embedded systems suffer from most, and Apriorit’s expert tips to protect embedded sys...

Medical Device Software Development 101: Types, Use Cases, and Software Development Tips
Learn all you need to know about medical device software development: device types and use cases, development steps, practices, and challenges.

How Does AI Revolutionize the Energy Sector? Benefits, Use Cases, Implementation Tips
Learn everything about using AI in the energy sector: its applications, benefits, implementation challenges, and why we can help you adopt it.

How to Create a Reliable SaaS Accounting Solution: Core Characteristics, Architectural Components, and Features
Discover how to create accounting software as a SaaS solution. Explore key features, architectures, and best practices to build a competitive product...
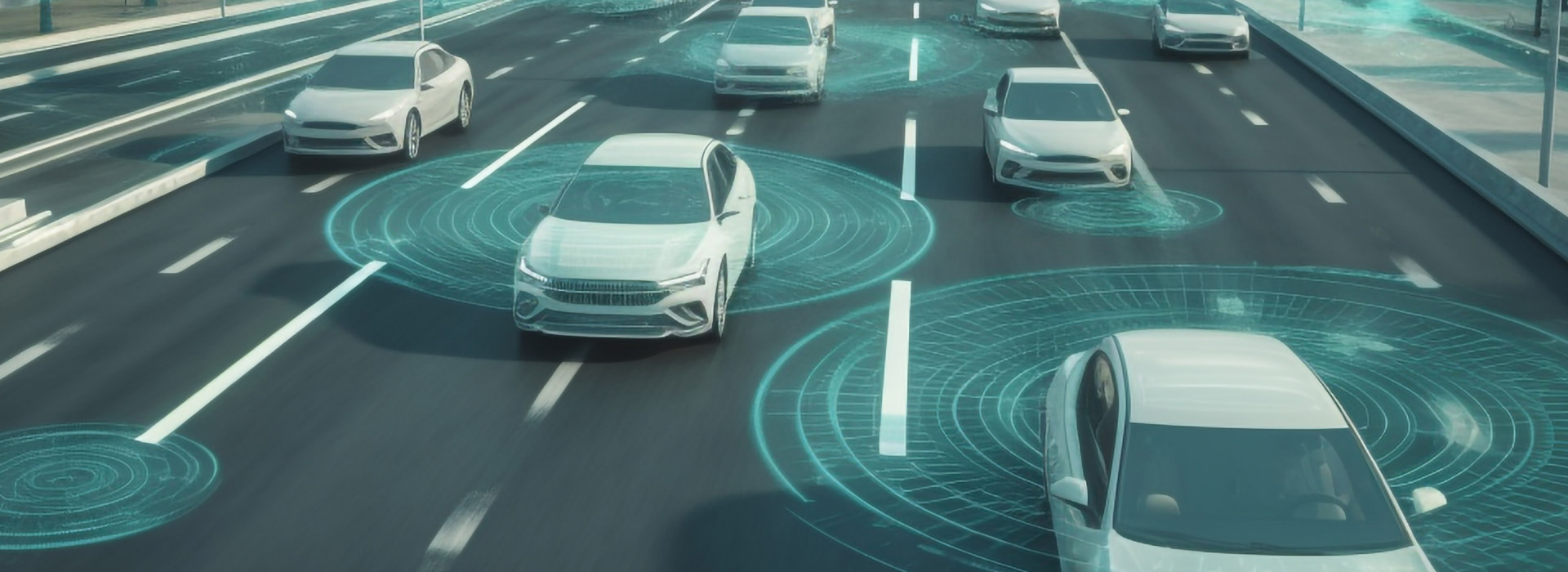
Data Analytics in the Automotive Industry: Use Cases, Trends, and Challenges
Learn how to use data analytics in the automotive industry, gain business benefits from it, and enhance analytics with AI, ML, and big data algorithms...


