Can a blockchain strengthen the security of your solutions? With features like decentralization, smart contracts, and tokenization, a blockchain can offer robust ways to protect your data and automate cybersecurity efforts. But what exactly is the role of blockchain in cybersecurity, and can it really provide robust protection for all businesses?
In this article, we take a closer look at the benefits and challenges of blockchain cybersecurity and analyze the possible impact of the blockchain on the cybersecurity of different solutions. We also overview key blockchain use cases in cybersecurity and demonstrate its application based on real-life examples from different industries.
Contents:
Using the blockchain for cybersecurity: benefits and considerations
The blockchain has endless applications for organizations in healthcare, the public sector, logistics, finance, etc. Apart from unique functionality, the blockchain also provides next-level security due to its inherent qualities like decentralization and cryptography. Let’s look at the main advantages of this technology for protecting software.
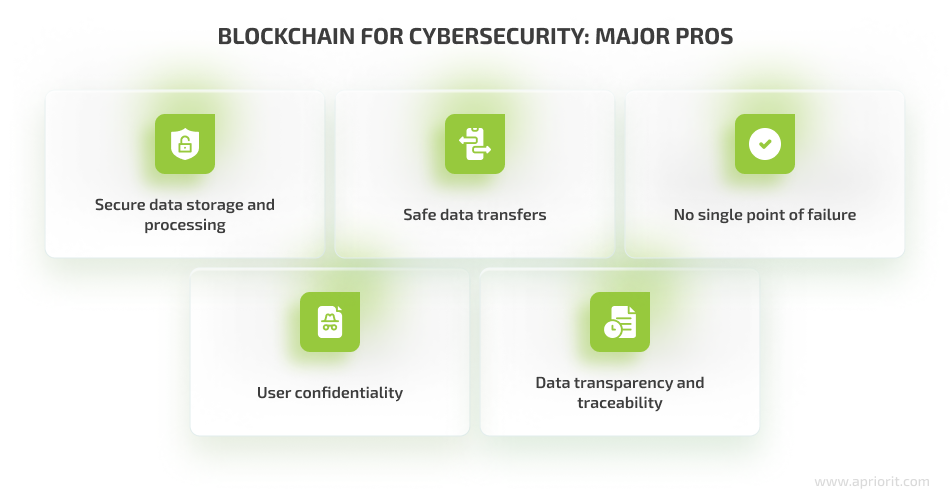
Secure data storage and processing — Blockchain records are immutable, and any change recorded on the blockchain is transparent and can’t be modified. Therefore, data stored on a blockchain is protected better than traditional digital or paper-based records.
Safe data transfers — The blockchain enables fast and secure transactions involving data and finances. Smart contracts, which are an integral part of blockchain technology, contribute to security by automatically executing agreements, reducing the risk of human error and potential points of vulnerability.
No single point of failure — Permissionless blockchain systems are decentralized and, therefore, more resilient than traditional systems. To affect the operation or security of the whole blockchain, a malicious actor has to compromise 51% or more of network nodes. This means that even in the case of DDoS attacks, the system will operate normally thanks to multiple copies of the ledger. Private blockchains, however, can’t offer this advantage.
Data transparency and traceability — The blockchain improves cybersecurity by having digitally signed and time-stamped transactions and allowing network users to easily trace the transaction history and review accounts at any historical moment. This feature also allows a company to have valid information about its assets or product distribution.
User confidentiality — The confidentiality of blockchain network participants is high due to the use of public key cryptography to authenticate users. However, some blockchain-based startups go a step further and improve this technology. For instance, Guardtime developed a Keyless Signature Infrastructure (KSI) that allows users to verify signature validity without disclosing keys.
Related project
Evaluating Smart Contract Security for Decentralized Finance (DeFi)
Explore how the Apriorit team performed a comprehensive security audit for a DeFi project.

What to consider before using the blockchain for cybersecurity
While the blockchain has rich potential as a cybersecurity measure, this technology is also associated with several challenges. Let’s look closer at the key drawbacks of the blockchain that you need to take into account before deciding to strengthen the security of your solution with this technology.
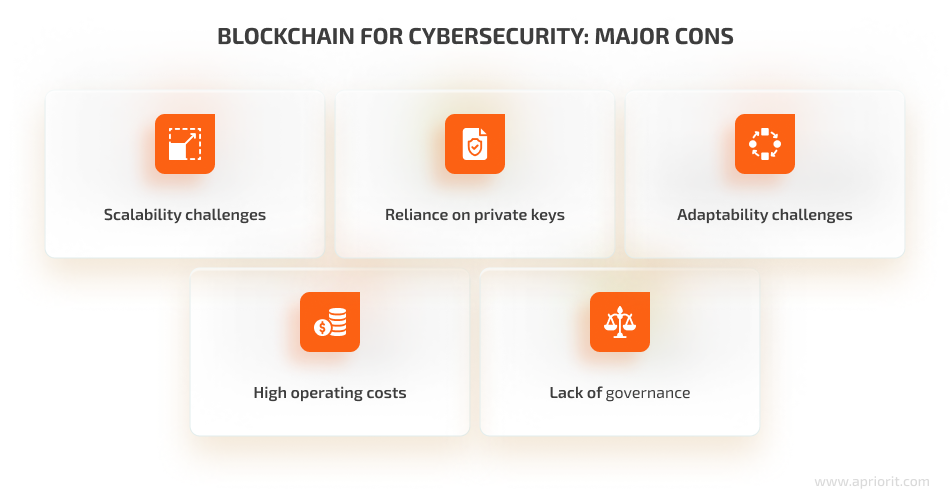
Scalability challenges — Blockchain networks have different limits for block volume and number of transactions per second. From the cybersecurity standpoint, your blockchain system must handle all security-related transactions and data to ensure secure data storage without harming your product’s performance. We recommend checking the scalability of the blockchain platform you want to use as the basis for your solution and considering your expected load in advance.
Reliance on private keys — Blockchains rely on private keys, which are long sequences of random numbers automatically generated by a wallet. Private keys are used for interacting with the blockchain and ensure security. If a user loses their private key, critical encrypted data could become permanently inaccessible, making key management a critical security concern.
Adaptability challenges — Though blockchain technology can be applied to almost any business, companies may face difficulties integrating it. It’s quite challenging to secure supply chain systems, for instance, as it may take much time to re-implement supply chain logic using a blockchain. Blockchain applications can also require replacing existing systems, so companies should consider this before implementing blockchain technology.
High operation and customization costs — A blockchain network requires substantial computing power and storage capacity. This may lead to higher marginal costs in comparison with existing non-blockchain systems. At Apriorit, we always focus on the cost-efficiency and business value of our blockchain-based solutions.
Lack of clear governance — The operation and use of blockchain technology isn’t well regulated globally. Although many countries are focusing on blockchain and cryptocurrency laws and regulations, requirements are changing and evolving, making it hard for vendors to implement them. You need to constantly track changes in laws and regulations to make sure your system complies with those applicable in your region and industry.
These are the main challenges you need to consider when deciding to implement blockchain technology to improve your product’s cybersecurity. However, the final scope of possible disadvantages will vary depending on the industry you operate in and the additional tasks you want to solve with the help of the blockchain.
Let’s take a closer look at the main use cases of blockchain in cybersecurity.
Need to secure your product?
Leverage Apriorit engineers’ expertise to get bullet-proof blockchain-based protection from cyber threats.
Top blockchain applications for cybersecurity
The blockchain is a versatile technology you can apply to achieve various cybersecurity goals. However, unlike cybersecurity scripts, which you can integrate into separate parts of your software, blockchain implementation usually requires a comprehensive approach. This means that your whole software system and even business operations may need significant changes in order to benefit from the blockchain’s security features.
Let’s look at the main ways you can use a blockchain to protect your product from cyber threats and make your business more reputable, secure, and trustworthy.
1. Validating ownership and tracking records
The blockchain can validate ownership of digital assets, such as domains, intellectual property, or digital certificates, ensuring that only authorized parties can make changes.
For example, the real estate industry is adopting blockchains to validate property ownership, reducing fraud and disputes. StreetWire and ShelterZoom use this technology to simplify data management for real estate businesses.
You can also use blockchain-based ownership validation in supply chains to track and authenticate assets, ensure their integrity, and reduce the risk of counterfeiting.
The blockchain’s immutability makes it ideal for creating unchangeable audit trails, which can be used to track and verify activity within a system. For example, healthcare organizations use blockchain-based immutable audit trails for patient records, ensuring the integrity and security of medical data.
The blockchain technology in cybersecurity can also be useful for improving the safety and transparency of many government processes: tax collection, information governance, elections, etc.
Read also
Blockchain for Supply Chains: A Practical Example of a Custom Network Implementation
Learn how blockchain technology can improve today’s supply chain management routines.

2. Decentralized identity management
A blockchain can be used to record and verify the identity and integrity of users, devices, and software in a network. Each device or software component can have a unique identity on the blockchain, and their behavior can be monitored for any anomalies. This allows you to quickly detect unusual behavior that may be a sign of a breach or identity theft and address it before it causes harm to your system’s integrity.
By registering devices and software components on the blockchain, you can enforce identity-based access control. This will allow you to get more control over devices and software access to your product, reducing the risk of unauthorized access.
With a blockchain-based identity management system, individuals can control their digital identities and reduce the risk of identity theft. For example, Sovrin is a decentralized identity platform that uses the blockchain to give users control over their personal data. It is used in various applications, including self-sovereign identity verification.
A blockchain is also an ideal environment for zero-knowledge proofs — cryptographic techniques used to prove that a system stores a specific piece of information without revealing the actual information itself. It utilizes blockchain for cybersecurity and privacy and makes authentication safer. Zcash, a privacy-focused cryptocurrency, uses zero-knowledge proofs to enable private transactions while proving the validity of transactions to the network.
Related project
Enhancing Financial Data and Operational Security with a Tezos Wallet and dApp Audit
Explore how the Apriorit team audited a Tezos wallet and a decentralized application (dApp), discovered vulnerabilities, and created an action plan to fix them.
3. Secure data sharing and storage
The blockchain can be used for secure and tamper-proof data storage and sharing, providing confidentiality and integrity of sensitive information. Let’s look at some examples in detail.
Healthcare organizations use blockchains to securely manage medical data. For example, BurstIQ is a blockchain-based platform that helps healthcare organizations securely store patient data and share it between different departments and institutions in near real time. A blockchain can also help establish secure messaging services for fast and comfortable patient–institution communication on administrative matters and non-urgent medical cases.
A blockchain can store tamper-proof records of all operations and transactions for each product in the supply chain. Global giants like Walmart, BMW, and FedEx deploy blockchains to simplify the analysis of supply chain efficiency and operations.
The public sector uses blockchains to ensure election security. Blockchain-based voting systems provide transparent and tamper-resistant voting records. For example, Estonia successfully secured its voting system with a blockchain to prevent malicious actors from accessing citizen voting data.
Apart from securing voting records, a blockchain also helps to speed up vote counting and ensure the accuracy of results. As all records are immutable, tampering with electronic votes on a blockchain becomes almost impossible. However, maintaining the anonymity of a voter’s choice while validating voter identities may be a challenge.
IoT technology paired with the blockchain can result in more secure communication and data exchange between IoT devices by leveraging a tamper-resistant and decentralized ledger for device interactions.
In the financial sector, the biggest value of a blockchain is in its data immutability and transaction transparency. Storing transactions on the blockchain is more transparent and secure than keeping traditional digital or paper records. Some banking organizations, such as ING Group, use blockchains (particularly, zero-knowledge range-proof solutions) to protect the confidentiality of customer information. Q2, a virtual banking platform, uses a blockchain and machine learning to strengthen user data protection.
Read also
How to Improve Your Identity Verification with Blockchain: Tools and Practical Examples
Explore the benefits and challenges of using blockchain for identity verification. Get insights into system design, compliance implications, and how blockchain reduces fraud risks.

4. Security automation with smart contracts
Blockchain-based smart contracts can automate security procedures and actions, ensuring compliance and rapid response to security incidents. Ethereum-based smart contracts can automate security actions in decentralized applications (dApps) and blockchain systems, improving security by reducing human error. Smart contracts ensure fast, secure, and fully automatic execution of agreements between several parties.
For example, by combining blockchain technology and smart contracts, you can automate Distributed Denial of Service (DDoS) protection for your product by automatically restricting the number of requests or validating each network participant.
In the financial sector, smart contracts are leveraged to automate payment processing and validate transactions. These contracts enable the automatic execution of agreements when all conditions are met, reducing the risk of fraudulent activities. For instance, financial institutions like JPMorgan have explored using the blockchain and smart contracts for efficient and secure collateral settlements.
Companies like SMARTRealy and Propy leverage smart contracts to sell, buy, or rent property.
The role of blockchain in cybersecurity of supply chains lies in using smart contracts to automate the verification of goods and products, protecting your supply chain from counterfeit products and product tampering automatically, without any human involvement.
Conclusion
The blockchain offers rich opportunities for maintaining a high level of data safety thanks to reliable data encryption mechanisms, data integrity, network resilience, and scalability. As a result, switching from a traditional security system to a blockchain-based system can benefit organizations in almost any industry.
But as with any revolutionary solution, organizations should be ready to deal with potential complications when using a blockchain and cybersecurity to improve the protection of their products.
At Apriorit, we have a dedicated team of highly competent blockchain developers who know all the ins and outs of this promising technology. Get in touch with us and we’ll gladly assist you in turning your blockchain-related idea into a real-life product.
Need to protect your product?
Our team of experts can implement a robust blockchain-based cybersecurity strategy that will protect your product from cyber threats.




