Key takeaways:
- Telecom systems are highly targeted because they handle sensitive personal data and critical services like emergency communications and government networks.
- Their complexity, high load, and interconnected components create a large attack surface.
- AI and 5G introduce new risks on top of traditional threats like DDoS, phishing, malware, botnets, and insider abuse.
- Modernization must secure both legacy and cloud-native systems using zero-trust, secure SDLC, and hardened CI/CD pipelines.
- Effective cybersecurity in the telecom industry requires a holistic strategy rather than protecting individual components in isolation.
After government and administrative systems, cyber criminals target telecom more than any other sector — and not without reason.
Telecom software has to handle massive volumes of sensitive data, be always on, and support critical services. That combination makes even small security weaknesses costly — leading to outages, data exposure, fraud, and regulatory risk.
At the same time, advancements in AI and 5G give hackers new ways to target your systems. To combat these threats, you need to understand what to secure — and how. This is exactly what our article is about.
If you’re a CTO, an engineering leader or a product owner who seeks to build telecom systems that are truly resilient in the face of cyber attacks, this article is for you. We explore how cybersecurity threats impact different parts of telecom systems in practice and what engineering teams can do to reduce risk without slowing delivery.
Contents:
Telecom: A high-value target for attackers
Telecom systems are unimaginably complex. For software architects, business leaders, and engineers, this complexity is a challenge. For hackers, it’s an opportunity.
Malicious actors, ranging from individual hackers to state-sponsored groups, continually seek to exploit vulnerabilities within telecom software for financial gain, espionage, or sabotage.
In 2025 alone, a total of 444 incidents were observed by Cyble, involving breaches, leaks, ransomware, access sales, and hacktivism. According to QBE’s research, telecom ranked as the second most attacked sector after government and administrative systems.
Key factors that increase cybersecurity risk for telecoms include:
- Massive volumes of customer and signaling data. Telecom systems process and store large amounts of sensitive customer, billing, and signaling data. This makes them high-value targets for attackers seeking financial gain, intelligence, or leverage through data exposure.
- Strict continuity requirements. Telecom services are expected to be available 24/7. Even short outages can result in immediate revenue loss, service-level agreement violations, and reputational damage, leaving little room to respond to attacks without business impact.
- Legacy and cloud-native technology stacks. Telecom platforms often combine legacy protocols and monolithic systems with cloud-native, containerized components. This mix increases risk due to inconsistent security controls, outdated assumptions, and complex trust boundaries.
- Highly interconnected ecosystems. Operations support systems (OSS) and business support systems (BSS), network functions, vendors, roaming partners, regulators, and customer systems are tightly integrated through APIs and data exchanges. A weakness in one integration can become an entry point into the wider telecom environment.
- Proliferation of IoT systems and 5G connectivity. IoT and 5G dramatically increase the number of connected devices and network entry points. Each device, service, or slice expands the attack surface and raises the risk of large-scale abuse or lateral movement.
- Advancements in AI. Artificial intelligence is increasingly used within telecom systems for automation and optimization. One of the current telecom cybersecurity trends is using AI to detect fraud — but attackers also use it to commit fraud. For cyber criminals, AI enables faster reconnaissance, more convincing fraudulent schemes and social engineering, and automated exploitation. It also introduces new risks for organizations through AI-driven workflows and decision logic.
- Transition to post-quantum cryptography. Telecom organizations are starting to implement quantum-ready algorithms and replace current encryption. But if done rashly, this can cause interoperability issues and give an opening for hackers to exploit.
All these factors make telecom vulnerable to cybersecurity attacks. Let’s look at the most frequent cybersecurity threats in the telecom industry.
Build a bullet-proof telecom system
Reach out to our cybersecurity experts to get a secure telecom solution that is always on for your users and never accessible to hackers.
Main cybersecurity risks in telecom software
As telecom networks become more interconnected and automated, the frequency and complexity of cyber attacks are rising sharply.
Below are the most common types of attacks targeting telecom software:
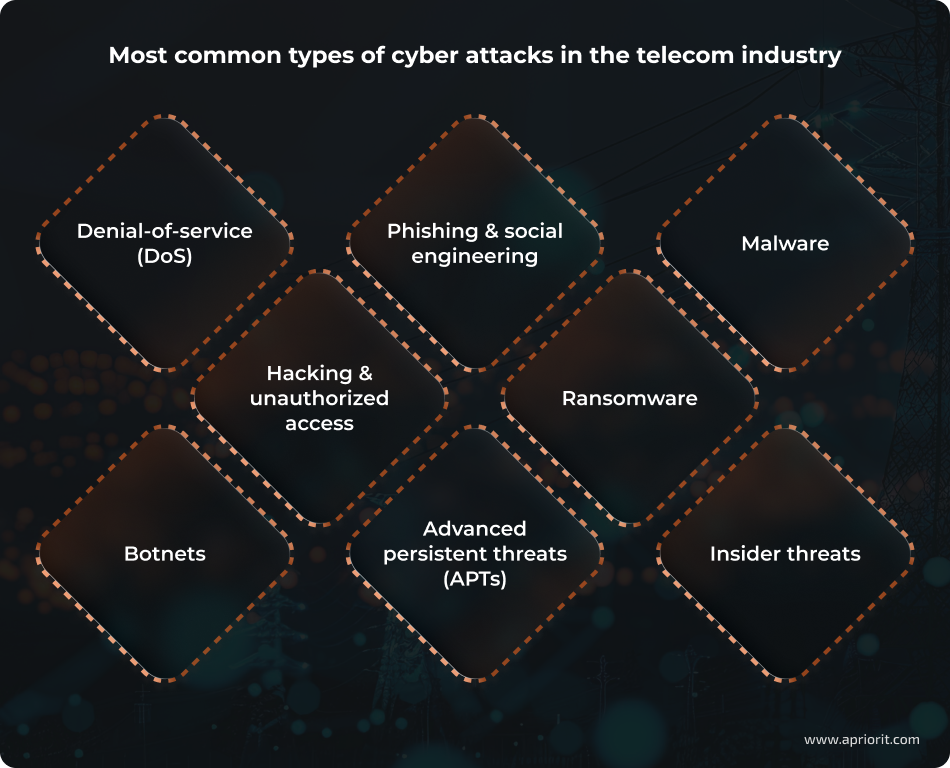
- Denial-of-service (DoS) attacks. Distributed or targeted DoS attacks flood networks or services with traffic, overwhelming capacity and causing outages. Telecom infrastructure is consistently hit by network-layer DDoS traffic, with attack volumes and frequency climbing year over year.
- Phishing and social engineering. Phishing remains a primary vector for initial access. Attackers use email, SMS, and social engineering to steal credentials or trick telecom employees into executing malicious actions. This type of attack is widely used to compromise user accounts, provide a foothold in internal telecom systems, or bypass authentication controls.
- Malware. Trojans, spyware, and automated attack frameworks compromise endpoints or telecom servers, allowing attackers to extract data, manipulate workflows, or launch secondary attacks. In the telecom sector, tools like BPFDoor and GhostSpider have been deployed specifically to maintain long-term, stealthy persistence within carrier infrastructure.
- Hacking and unauthorized access. Attackers exploit vulnerabilities, weak credentials, or configuration flaws to gain unauthorized access to systems such as customer databases, network management platforms, or control interfaces. Telecoms are particularly exposed through internet-facing network equipment like routers and VPN gateways.
- Ransomware. In 2025, telecom firms experienced roughly a fourfold rise in reported ransomware cases, reflecting their value as targets due to large datasets and critical infrastructure roles. These attacks can encrypt systems, disrupt services, and lead to costly recovery efforts.
- Botnets. Attackers use networks of compromised devices for large-scale attacks such as DDoS amplification, credential stuffing, and automated scanning. Botnets are consistently used as tools in some of the largest DDoS events recorded, underscoring how infected consumer or IoT devices can be leveraged against telecom networks.
- Advanced persistent threats (APTs). These stealthy, long-term campaigns are designed to infiltrate and maintain access to critical systems. In telecom, APT groups often target backbone infrastructure to enable espionage, data interception, or long-term positioning for strategic leverage.
- Insider threats. Not all threats come from outside the organization. Employees or contractors can misuse legitimate access to sensitive systems, manipulate billing or provisioning logic, or leak credentials. These threats are particularly dangerous in complex telecom environments with many privileged users and automated systems.
While these risks are common across the telecom industry, they don’t affect all systems equally. Impact and attack surface vary by subsystem, depending on architecture, access models, and integration patterns.
Read also
Cloud Application Security Best Practices: Data Safety and IT Compliance Challenges
Strengthen your cloud environment with proven compliance strategies. Explore practical steps to reduce risks and align your infrastructure with key security standards.

High-risk areas by telecom system component
Each component in telecom software plays its own role in a system — whether it’s enabling service delivery, protecting revenue, or keeping the network stable. Because of this, some components naturally draw more attention from attackers.
To show how different risks play out across the ecosystem, let’s break down the most vulnerable telecom components, the threats they typically face, and which parts of each subsystem require the most attention.
Table 1. High-risk areas by telecom system component
| Telecom component | Common threats | Components to secure |
|---|---|---|
| OSS/BSS platforms | – Business logic abuse – AI-assisted fraud – Attacks via insecure integrations – Abuse of privileged internal access | – Billing engines and provisioning workflows – API integrations – Data synchronization and reconciliation processes – Access control and audit logs – Administrative and support tooling |
| Network management & automation systems | – Exploitation of automation pipelines – AI-driven probing of orchestration/APIs – Privilege escalation | – Orchestration and automation platforms – Access controls – Network management APIs – Admin consoles and configuration databases |
| VoIP, IMS & SIP-based systems | – SIP flooding – Malformed signaling messages – Call hijacking – Signaling-layer DoS – AI-generated voice spoofing – Fraudulent call routing | – SIP/IMS protocol parsers and signaling engines – Call routing and admission control systems – Rate-limiting and traffic-shaping mechanisms – Interconnect authentication modules |
| 5G core, NFV & cloud-native functions | – Lateral movement between virtual network functions – Exploitation of container or orchestration vulnerabilities | – Kubernetes clusters and service meshes – Orchestration pipelines – VNFs and container images – CI/CD pipelines – Infrastructure as code templates and repositories |
| Customer-facing apps & self-service portals | – Account takeover – AI-driven credential stuffing – API abuse – Sensitive data leakage via misconfigured access controls | – Authentication and session management modules – API endpoints and backend services – Sensitive data storage and access controls – Rate limiting and bot detection mechanisms |
OSS/BSS platforms
OSS/BSS platforms encode complex business logic that governs billing, provisioning, and service lifecycle management.
These systems are often attacked without exploiting classic technical vulnerabilities. Instead, attackers focus on abusing legitimate workflows, predictable automation, and overly permissive access models.
When combined with multiple integrations and privileged operational tooling, even small gaps in logic can lead to revenue loss, service misuse, or large-scale data exposure.
Main threats for OSS and BSS systems include:
- Business logic abuse, such as billing manipulation or provisioning errors triggered through valid but misused workflows
- AI-assisted fraud, where attackers systematically probe workflows to discover exploitable edge cases
- Attacks through insecure integrations with CRM, billing, payment, or ERP systems
- Abuse of privileged internal access, including misconfigured roles or overpowered support and operations accounts
Components to secure:
- Billing engines and provisioning workflows
- CRM, billing, payment, and ERP system integrations
- Data synchronization and reconciliation processes
- Access control and audit logs
- Administrative and support tooling used for manual overrides
Network management and automation systems
These systems control how the telecom network behaves at scale. Designed for efficiency and speed, they can be dangerous when misused. A single compromised automation workflow or orchestration account can trigger configuration changes across large parts of the network, leading to outages, security gaps, or persistent attacker access.
Network management systems can expose high-privilege APIs and control planes, often with insufficient segmentation between read-only monitoring and write-level configuration actions.
The main threats for this component of a telecom system include:
- Exploitation of automation pipelines to push malicious or unsafe configurations
- AI-driven probing of misconfigured orchestration tools or management APIs
- Privilege escalation through orchestration platforms, leading to broad network control
Components to secure:
- Orchestration and automation platforms
- Access controls
- Network management APIs and interfaces
- Admin consoles and configuration databases
VoIP, IMS, and SIP-based systems
VoIP, IMS, and SIP-based systems are exposed by design: they must accept and process signaling traffic in real time to deliver voice services. This makes them particularly sensitive to malformed messages, traffic spikes, and trust assumptions between interconnected networks.
Attackers can exploit weaknesses in protocol handling, rate control, and interconnect trust models to disrupt services, hijack calls, or commit fraud. Advances in AI-driven voice synthesis have also increased the effectiveness of voice-based fraud and social engineering attacks.
Main threats:
- SIP flooding and malformed signaling messages that degrade or disrupt services
- Denial-of-service conditions caused by high-rate or invalid signaling traffic
- AI-generated voice spoofing used for fraud or social engineering
- Fraudulent call routing or bypassing of call restrictions
Components to secure:
- SIP/IMS protocol parsers and signaling engines
- Call routing and admission control systems
- Rate-limiting and traffic-shaping mechanisms for signaling
- Interconnect authentication modules
Related project
Improving a SaaS Cybersecurity Platform with Competitive Features and Quality Maintenance
Learn how we implemented new features in a low-level vulnerability detection engine and improved the platform’s stability and user experience.

5G Core, NFV, and cloud-native network functions
5G Core (5GC) and NFV environments rely on cloud-native architectures, containerization, and software-defined networking. While this enables scalability and rapid innovation, it also introduces new risks related to orchestration complexity, shared infrastructure, and supply chain dependencies.
Attackers frequently aim to gain an initial foothold in a single workload and then move laterally across virtualized network functions.
Main threats include:
- Lateral movement between virtual network functions and cloud-native workloads
- AI-accelerated exploitation of container, orchestration, or control-plane vulnerabilities
Components to secure:
- Kubernetes clusters, service meshes, and orchestration pipelines
- Virtual network functions (VNFs) and container images
- CI/CD pipelines
- Infrastructure as code (IaC) templates and configuration repositories
Customer-facing apps and self-service portals
Customer-facing applications are often the most visible and frequently attacked parts of a telecom platform. They expose authentication flows, APIs, and backend services directly to the internet, making them prime targets for automated abuse and data extraction.
Flaws in these apps allow attackers to take over accounts, scrape sensitive data, or abuse backend services.
Main threats include:
- Account takeover through weak authentication or session management
- AI-driven credential stuffing and brute-force attacks
- Abuse of APIs exposed through mobile or web clients
- Leakage of sensitive data caused by misconfigured access controls
Components to secure:
- Authentication and session management modules
- API endpoints and backend services
- Sensitive data storage and access controls
- Rate limiting, bot detection, and abuse prevention controls
So far, we’ve discussed telecom system components and threats that are specific to them. But how do you actually protect these components? What should you add to your telecom cybersecurity strategy to make sure every part of your system is reliably secured? We explore best practices in the next section.
Read also
9 Emerging Cybersecurity Trends for 2026 to Futureproof Your Product
Anticipate emerging cyber threats before they disrupt your roadmap. Discover key security trends shaping software development and learn how to adapt your strategy to protect products and business value.

A holistic security strategy for telecoms
Telecom systems are too complex and high-risk to rely on isolated security tools and reactive fixes. True resilience requires a cohesive security strategy embedded into architecture, development, and operations.
In this section, we outline the core outcomes of an effective cybersecurity strategy for telecom platforms — and practical actions that help you achieve them.
Table 2. A security strategy from Apriorit
| Objective | Practices to implement |
|---|---|
| Keep your systems on 24/7/365 | – Network segmentation – Encryption and secure communication among all system components – Continuous monitoring and anomaly detection |
| Sustain high loads safely | – Security controls – Behavior-based detection – Rate-aware monitoring |
| Stay secure and live during modernization | – Zero-trust and least-privilege – Secure CI/CD – Secure SDLC – Incremental approach to modernization |
| Keep your APIs and integrations safe | – Strong API authentication and authorization – Multi-factor authentication and secure session management – Consistent validation and access control |
| Prevent revenue loss from fraud and insider abuse | – Workflow and business logic testing – Fuzzing and edge-case testing – Auditing and traceability |
| Detect threats before they turn into breaches | – Continuous infrastructure monitoring – Anomaly detection – Correlation of technical and business signals |
To keep your systems on 24/7/365
In telecom, outages are rarely isolated. A misconfigured network function, compromised admin account, or cyber attack can quickly propagate across interconnected systems.
Because core services depend on tightly coupled components, even a localized failure can escalate into a large-scale disruption.
This means that your security architecture must be designed for controlled degradation. The priority is to contain incidents, limit lateral movement, and ensure that when one subsystem fails or is compromised, the rest of the platform continues operating safely.
To achieve this, you need:
- Network segmentation to prevent failures or attacks from cascading
- Encryption and secure communication among all system components
- Continuous monitoring and anomaly detection to spot early signs of disruption
When implemented correctly, these measures allow your services to degrade gracefully under attack instead of failing outright, protecting both revenue and reputation.
Apriorit expert advice: Assume a breach will happen somewhere and design your systems so it cannot spread. Test failover and isolation mechanisms under simulated attack conditions — not just during routine performance testing.
To safely sustain high loads
Even in the absence of an attack or adverse situation, telecom environments operate at extreme scale. The challenge is ensuring that security mechanisms themselves do not become the weakest link under peak load.
Protection must be performance-aware and include:
- Security controls designed for high-throughput environments
- Behavior-based detection instead of static rules
- Rate-aware monitoring that distinguishes abuse from legitimate spikes
Apriorit expert advice: Test your security logic under realistic load. Validate that detection systems remain accurate at peak capacity and that automated protections do not unintentionally disrupt legitimate traffic.
To stay secure and live during modernization
The bigger the system, the riskier it is to modernize. That’s why many large businesses delay modernization, getting lost in outdated APIs, old workflows, and legacy systems.
You need not only to secure the new technology but also to integrate it in a way that doesn’t disrupt your current operations. To achieve secure modernization while keeping your telecom systems running, you need to implement:
- Zero-trust and least-privilege approaches to access across legacy and modern components
- Secure CI/CD pipelines and container scanning to prevent vulnerable artifacts from reaching production
- Secure SDLC practices, including threat modeling for new components and integrations
- Incremental hardening of both legacy and new components in parallel
Apriorit expert advice: Before connecting legacy and new systems, clearly define who can access what and where data flows. Make sure new components are built with modern security practices and do not rely on outdated permissions, assumptions, or controls from older systems.
To safeguard your APIs and integrations
Telecom platforms depend on APIs to connect OSS/BSS, billing, provisioning, partners, and customer-facing services. Each integration expands the attack surface.
To mitigate potential vulnerabilities, you need:
- Strong authentication and authorization for internal and external APIs
- Multi-factor authentication and secure session management for admin and support access
- Consistent validation and access control across all integrated platforms and systems
Apriorit expert advice: Our recommendation is to inventory all APIs — including internal — and classify them by exposure and privilege level. Test them for authorization logic weaknesses and inconsistent enforcement across services.
Read also
Securing APIs for Your Software: 6 Best Practices
Discover proven security practices that help you safeguard integrations, ensure reliable performance, and maintain customer trust.

To prevent revenue loss from fraud and insider abuse
In telecom, subtle manipulation of workflows, pricing logic, or provisioning rules can quietly erode revenue or create regulatory exposure.
Addressing this requires:
- Workflow and business logic testing for billing, provisioning, and automation
- Fuzzing and edge-case testing for protocol-heavy and event-driven systems
- Auditing and traceability for high-impact actions
Apriorit expert advice: While vulnerability scanning goes a long way, in the case of fraud, it’s often not enough. We recommend simulating misuse scenarios and abuse cases during testing. Make sure that privileged actions are traceable and that overrides cannot occur without accountability.
To detect threats before they turn into breaches
In distributed telecom systems, early signals are often subtle: unusual configuration changes, abnormal billing behavior, or traffic patterns that look legitimate at first glance. Detection must therefore combine technical and business context.
To catch these signs early, you need:
- Continuous monitoring across infrastructure, applications, and workflows
- Anomaly detection tuned to telecom-specific patterns
- Correlation of technical and business signals
Apriorit expert advice: Monitor not only CPU spikes and failed logins but also unusual billing adjustments, abnormal provisioning activity, or sudden changes in call routing patterns. Correlate these business events with technical logs to detect fraud and abuse early. After every incident, update access rules, workflows, and validation logic so the same scenario cannot be repeated.
How can Apriorit help secure your telecom software?
With over 20 years of cybersecurity expertise and deep system-level and network engineering experience, Apriorit helps telecom vendors and operators secure complex, high-load, distributed environments — from kernel-level components to cloud-native infrastructures.

With Apriorit, you get:
- An inherently secure telecom solution from day one. We design and build systems with security embedded into architecture, communication flows, and access models thanks to our secure SDLC approach to development.
- A practical, end-to-end security strategy. Our software architects assess your architecture, identify high-risk components, and define mitigation steps aligned with your business goals.
- Security audits with clear remediation plans. From architecture reviews and threat modeling to penetration testing, fuzzing, and configuration analysis, we show you where the weaknesses are and guide you through fixing them safely and efficiently.
- Secure API integrations. Apriorit developers design and validate secure authentication, authorization, and data exchange mechanisms across OSS/BSS, billing, provisioning, partner integrations, and customer-facing services.
- Secure cloud and virtualization. Our cloud engineers configure and harden Kubernetes clusters, NFV infrastructure, CI/CD pipelines, and infrastructure as code to prevent misconfigurations and lateral movement.
- DevOps automation with built-in security controls. We integrate security checks, container scanning, and compliance validation directly into your delivery pipelines without slowing release cycles.
- Controlled modernization. Whether you’re migrating from legacy systems or introducing new components, we help you modernize incrementally while preserving availability and minimizing risk.
As a result of working with us, you get a resilient telecom solution that’s able to withstand operational stress, evolving threats, and rapid technological change.
Looking for cybersecurity experts who speak telecom?
Build resilient telecom software with security at its core. Entrust your project to a team of cybersecurity experts who have over 20 years of experience.
FAQ
What are the most common cybersecurity risks in telecom software?
<p>The main types of cyber attacks on telecommunications software include:</p>
<ul>
<li>Denial-of-service attacks that take systems offline</li>
<li>Phishing or credential attacks targeting admin and support accounts</li>
<li>Malware infections</li>
<li>Business logic abuse in billing and provisioning</li>
<li>API abuse</li>
<li>Insider threats</li>
</ul>
<p>AI-driven attacks and automated fraud are rising as well.</p>
<p>Essentially, any vulnerability that lets an attacker disrupt services, steal sensitive data, or manipulate workflows is a key risk in telecom environments.</p>
Which telecom components are the most common targets for attackers?
<p>Attackers often focus on OSS/BSS platforms (billing, provisioning, CRM), network management and orchestration systems, VoIP/SIP/IMS components, customer-facing apps, and 5G/NFV cores. They also target APIs, CI/CD pipelines, and cloud infrastructure.</p>
<p>In short, any component that handles sensitive data, controls network behavior, or interacts with external systems is a prime target because it can give attackers access to customer information or help attackers cause revenue loss or service disruption.</p>
What compliance and security frameworks should telecom software vendors and operators consider?
<p>Telecom vendors should follow standards like ISO 27001 for information security, NIST Cybersecurity Framework for operational protection, and ETSI/3GPP guidelines for 5G and network function security.</p>
<p>If you operate in the European Union, you need to comply with the GDPR. For other locations, follow all relevant local privacy laws and regulations. PCI DSS compliance is important if you deal with billing or payment data.</p>
<p>These frameworks provide a structured way to manage risk, implement controls, and demonstrate to regulators and partners that your systems are secure.</p>
Which telecom data is most sensitive and needs extra protection?
<p>The most critical data includes customers’ personally identifiable information (names, IDs, contact info), authentication credentials, billing records, call and messaging metadata, network configuration data, and API keys.</p>
<p>These are of high value because attackers can use them for fraud, identity theft, or service disruption. Protect critical data with encryption, strict access controls, audit logging, and monitoring to catch unauthorized access quickly.</p>
How can we reduce risk from third-party vendors and integrations?
<p>Start by auditing all vendors and their access levels. Require secure APIs, authentication, and encrypted communication. Limit privileges to only what’s needed, and monitor activity continuously.</p>
<p>We also recommend conducting regular security assessments or penetration tests on your integrated systems. Essentially, treat every integration as a potential attack path, and make sure you can detect, isolate, and remediate issues before they impact your platform.</p>


